In an era where digital innovation intersects with escalating cyber threats, the United States has unveiled a comprehensive approach to cybe...
In an era where digital innovation intersects with escalating cyber threats, the United States has unveiled a comprehensive approach to cybersecurity that emphasizes deterrence and resilience. The latest national cyber strategy, released by the White House in March 2026, outlines six pillars designed to counter adversaries while safeguarding critical infrastructure and emerging technologies like Web3 and blockchain. This framework arrives at a pivotal moment, as cyberattacks on decentralized systems and essential services continue to surge, demanding proactive defenses from governments, businesses, and individuals alike.
Web3, with its promise of decentralized finance, smart contracts, and blockchain-based applications, represents a frontier of opportunity but also vulnerability. As adoption grows, so do the risks from state-sponsored hackers and criminal networks targeting these ecosystems. Drawing from official documents and recent threat intelligence, this article explores the strategy's implications through a structured lens: threat models, attack paths, detection signals, and controls. By focusing on practical insights, it aims to equip readers with an understanding of how this policy can bolster security in an interconnected world.
Understanding the Threat Model: Adversaries Targeting Emerging Tech
The US cyber strategy identifies nation-state actors, such as China and North Korea, as primary threats, alongside cybercriminals exploiting emerging technologies. For instance, North Korean hackers linked to the Lazarus group were responsible for 76% of major crypto thefts in 2025, stealing over $3.4 billion through sophisticated social engineering and supply chain compromises. This data, sourced from Chainalysis's 2025 report, underscores how adversaries view Web3 as a lucrative target for funding illicit activities.
In critical infrastructure, threats manifest as disruptions to power grids, financial systems, and transportation networks. A 2025 study by Claroty revealed that 91% of operational technology (OT) environments in critical sectors experienced breaches over the past 18 months, often initiated by ransomware or state-backed intrusions. These attacks exploit vulnerabilities in interconnected systems, where Web3 integrations-like blockchain for supply chain tracking-can inadvertently expand the attack surface if not secured properly.
🚨 US Cyber Strategy Targets Adversaries, Critical Infrastructure, and Emerging Technologies Trump’s Cyber Strategy calls for stronger deterrence against cyber adversaries, modernization of federal networks, protection of critical infrastructure, and investment in technologies such as AI and post-quantum cryptography.
— xkzDB (@xkzdb) March 7, 2026
One non-obvious insight emerges from synthesizing these sources: while traditional threats focus on centralized systems, the decentralized nature of Web3 amplifies risks through "bridge attacks," where hackers exploit cross-chain protocols to siphon funds. The strategy's emphasis on sustaining superiority in blockchain and quantum computing addresses this by promoting US-led innovations, potentially reducing foreign dependencies that adversaries leverage.
State Actors vs. Criminal Syndicates
State actors prioritize espionage and disruption, as seen in China's reported use of AI to map US critical infrastructure vulnerabilities. According to a February 2026 Financial Times report, the Pentagon is countering this with AI-driven cyber tools, aligning with the strategy's deterrence pillar. Criminal syndicates, meanwhile, favor financial gain, with ransomware payments in critical sectors reaching $1.1 billion in 2023-a figure still relevant today because attack vectors like phishing remain unchanged despite evolving tactics, as noted in the FBI's Internet Crime Complaint Center archives.
This dual threat model highlights the need for layered defenses, especially as Web3 blurs lines between financial and infrastructural assets.
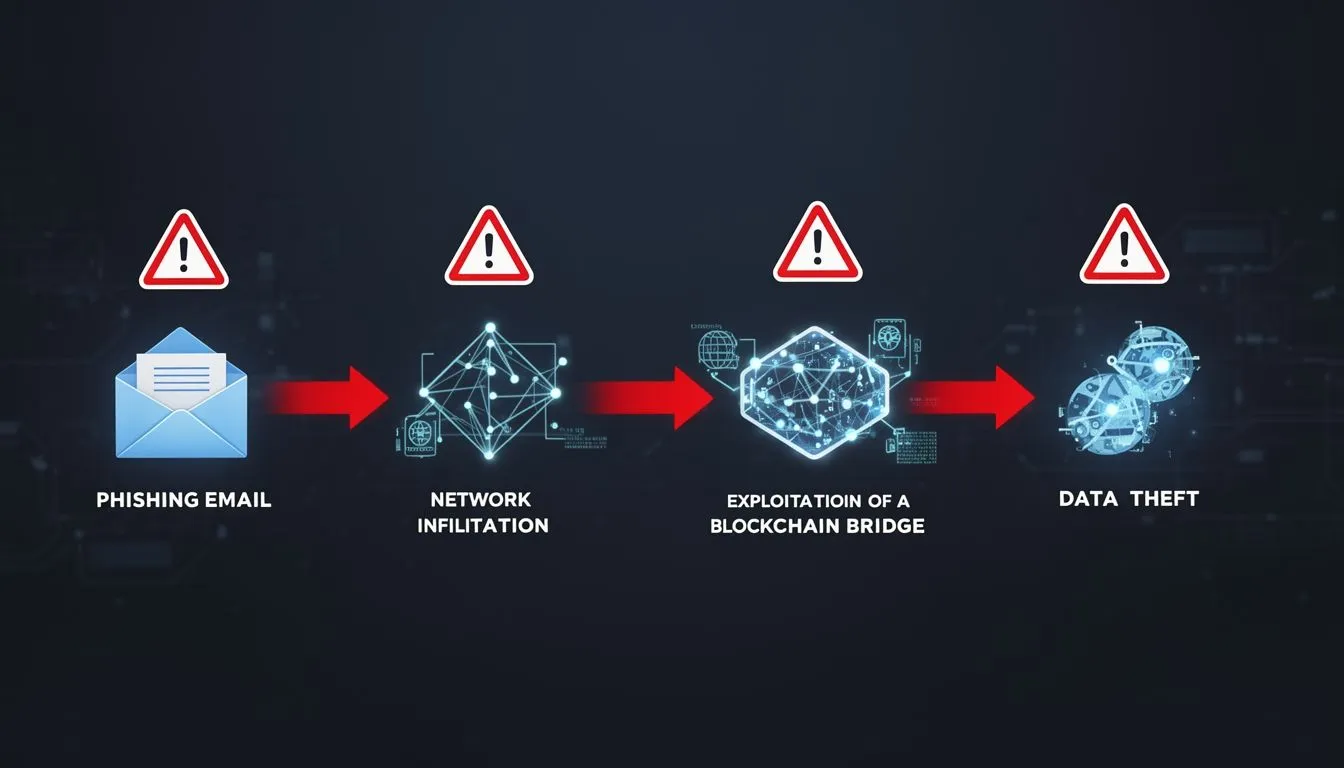
Mapping Attack Paths: From Initial Access to Exploitation
Attack paths in the context of the US cyber strategy often begin with social engineering or supply chain compromises, escalating to data exfiltration or system sabotage. In Web3, a common path involves phishing campaigns targeting wallet credentials, leading to unauthorized transfers. For critical infrastructure, paths exploit unpatched software or insider access, as evidenced by the 40% increase in phishing attacks on crypto users in the first half of 2025, per Kroll's Cyber Threat Intelligence report.
Consider a typical path: An adversary uses fake recruiter profiles on platforms like LinkedIn to distribute malware-laden "job applications," gaining network access. From there, they pivot to blockchain bridges or OT systems, exploiting weak authentication. The strategy counters this by advocating zero-trust architectures, which assume breach and verify every access request.
Real-World Implications for Web3 Integrations
In emerging tech, attack paths increasingly involve AI-enhanced tactics. The 2025 Certik Hack3d report documented $1.45 billion lost to supply chain attacks in Web3, where compromised dependencies in smart contracts enabled flash loan exploits. Critical infrastructure faces similar risks, with 71% of organizations reporting increased attack frequency in 2025, according to VikingCloud's cybersecurity stats.
Source validation here relies on cross-referencing official reports with independent analyses; for example, the White House strategy document directly informs these paths, while Chainalysis provides empirical data on blockchain-specific incidents, ensuring a balanced view.
Identifying Detection Signals: Early Warning Indicators
Detection signals serve as the first line of defense, alerting to anomalies before full breaches occur. In the strategy's framework, signals include unusual network traffic, anomalous login attempts, or spikes in computational resource usage-common in Web3 mining hijacks. For instance, the US Department of Defense's 2023 Cyber Strategy (still relevant as it forms the basis for ongoing operations, per its alignment with the 2026 update) emphasizes real-time monitoring through tools like endpoint detection and response (EDR).
Fresh data from the World Economic Forum's Global Cybersecurity Outlook 2025 indicates 72% of respondents noted rising cyber risks, with ransomware and AI-driven phishing as top signals. In critical infrastructure, signals might manifest as unauthorized API calls in blockchain-integrated systems, flagging potential exploits.
The Pentagon is reportedly in discussions with major AI labs about developing AI-driven cyber capabilities targeting China, including automated mapping of critical infrastructure networks such as power grids and utilities to identify vulnerabilities and support U.S. military planning, per FT.
— unusual_whales (@unusual_whales) February 27, 2026
A hypothetical scenario: Imagine a mid-sized energy firm adopting Web3 for transparent supply chain tracking. Detection signals trigger when irregular transaction volumes appear on their blockchain ledger, revealing a phishing-induced wallet drain. Early alerts from integrated monitoring tools allow swift isolation, preventing cascade to physical grid controls.
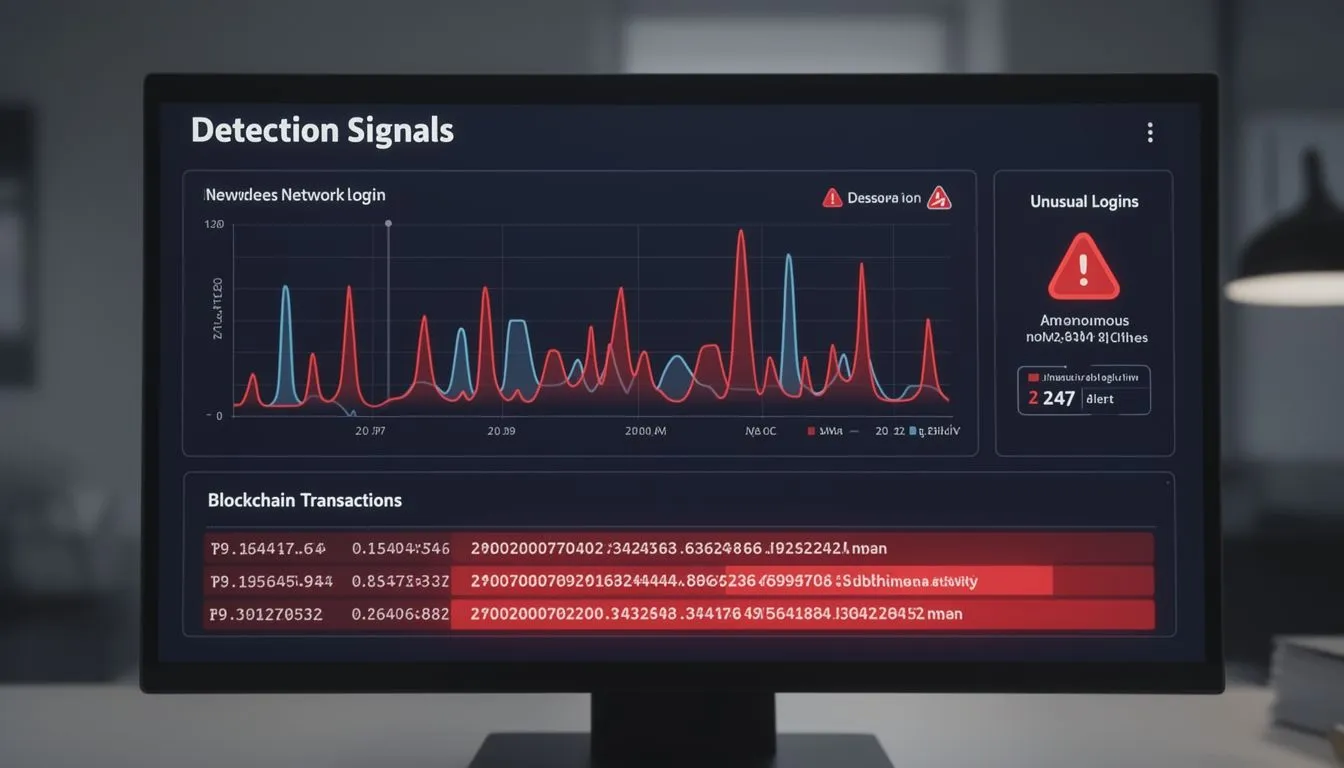
Integrating Signals into Daily Operations
Effective detection requires tools like SIEM (Security Information and Event Management) systems, which correlate signals across hybrid environments. The strategy's modernization pillar supports this by mandating AI for predictive analytics, helping spot patterns in emerging tech threats.
Implementing Controls: Defensive Steps and Prioritization
The core of the US cyber strategy lies in actionable controls, prioritizing deterrence through offensive capabilities while hardening defenses. For Web3 and critical infrastructure, controls focus on encryption, access management, and resilience planning.
Primary sources guide these: The official White House Cyber Strategy document details pillars like securing emerging technologies with post-quantum cryptography. CISA's 2024-2026 Cybersecurity Strategic Plan complements this with collaboration-focused controls. The 2023 DOD Cyber Strategy , though predating the latest, remains pertinent as it underpins defending forward tactics against persistent threats.
- [accordion]
- Key Defensive Insights
- Adopt zero-trust models to verify all access, reducing lateral movement in attacks. This is crucial for Web3 wallets, where multi-factor authentication can prevent 99% of credential-stuffing incidents, per recent Microsoft data.
- Non-Obvious Applications
- In blockchain environments, implement runtime monitoring to detect smart contract anomalies in real-time, synthesizing CISA guidelines with Web3-specific tools like those from Certik.
| Control | Objective | Implementation Priority |
|---|---|---|
| Post-Quantum Cryptography | Protect data against future quantum threats in emerging tech like blockchain | High - Deploy in federal and critical systems within 12 months |
| Zero-Trust Architecture | Limit breach impact by continuous verification | Medium - Phase in over 18 months for Web3 integrations |
| Supply Chain Risk Management | Secure dependencies in critical infrastructure and decentralized apps | High - Immediate audits for vendors |
| AI-Driven Threat Hunting | Proactively identify attack paths | Medium - Integrate with existing monitoring tools |
These controls prioritize concrete steps: Start with vulnerability scanning using tools like Nessus, then enforce least-privilege access. For Web3, mandate code audits before deployment, as 2025 saw billions lost from unaudited contracts. Training programs, per the strategy's workforce pillar, ensure teams recognize signals like phishing lures.

Building Long-Term Resilience
Beyond immediate controls, the strategy calls for international partnerships to standardize Web3 security, reducing global attack surfaces. Businesses should align by conducting regular penetration tests and incident response drills, turning policy into practice.
In conclusion, the US cyber strategy provides a roadmap for navigating threats to Web3 and critical assets, emphasizing collaboration and innovation. By implementing these defenses, stakeholders can foster a secure digital future amid evolving risks.




COMMENTS