Disclaimer: This article discusses sensitive cybersecurity topics involving nation-state threats and critical infrastructure. The content i...
Disclaimer: This article discusses sensitive cybersecurity topics involving nation-state threats and critical infrastructure. The content is provided for informational and educational purposes only and does not constitute professional advice. Organizations should consult qualified cybersecurity experts and follow official guidance from regulators for their specific environments.
When nearly 4,000 internet-exposed industrial control devices in the United States sit directly in the path of Iranian-affiliated threat actors, the stakes for IoT security shift from theoretical to immediate. These are not smart thermostats or consumer cameras. They are programmable logic controllers (PLCs) running water treatment plants, energy grids, and manufacturing lines. One misstep, and digital reconnaissance becomes physical disruption.
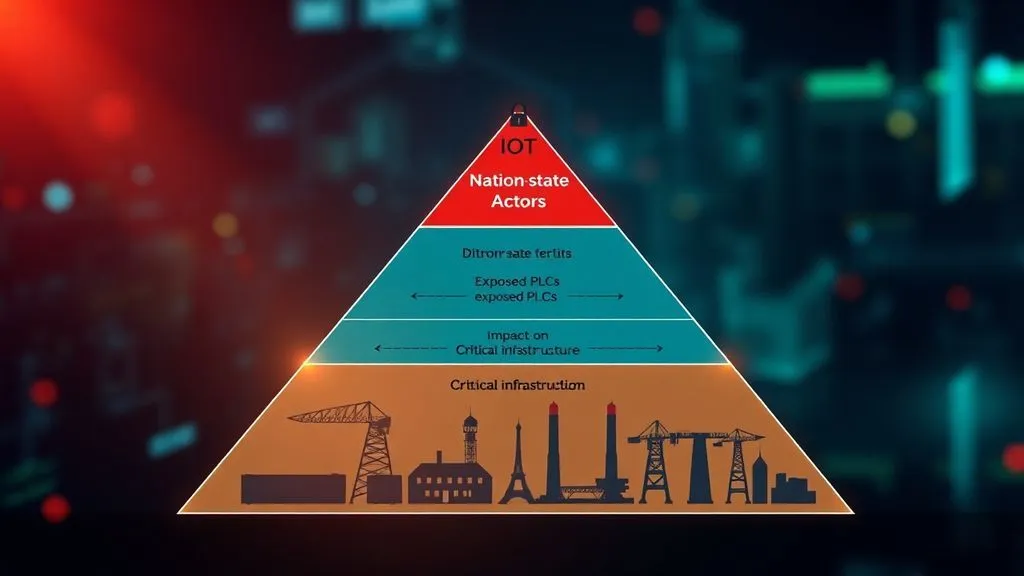
The Threat Model: Why Industrial IoT Draws Nation-State Attention
State-sponsored actors like those tied to Iran do not chase every connected gadget. They target systems where compromise yields strategic leverage. In this case, the model centers on operational technology (OT) environments that blend with IoT architectures. Attackers scan for devices that are publicly reachable yet lack modern safeguards, then exploit them to test safety systems or cause controlled outages.
Cross-referencing CISA's April 2026 advisory with independent internet-wide scans confirms the pattern. The advisory, issued jointly with the FBI, NSA, EPA, DOE, and US Cyber Command, details ongoing exploitation of Rockwell Automation/Allen-Bradley PLCs across critical sectors. Validation comes from matching indicators: EtherNet/IP services exposed on cellular networks, often in field-deployed setups far from corporate firewalls. This is not random scanning. It is deliberate mapping of assets that could influence physical outcomes.
What makes this model persistent? Industrial IoT devices rarely reboot, run legacy firmware, and sit behind air gaps that evaporated the moment remote monitoring became essential. Fresh 2025 data underscores the scale: global IoT devices faced an average of 820,000 attacks daily, a 46 percent jump from the prior year, with industrial sectors absorbing a disproportionate share.
Attack Paths: From Exposure to Disruption
The path is deceptively simple yet devastatingly effective. First comes reconnaissance. Tools identify devices responding on EtherNet/IP or common OT protocols. Many Rockwell PLCs self-identify publicly, and three-quarters of over 5,200 such systems worldwide sit in the US, often on cellular ASNs used for remote field operations.
Once located, attackers interact directly with project files or manipulate human-machine interface (HMI) and SCADA displays. In documented cases, this led to diminished PLC functionality and forced manual operations at water and energy sites. The Iranian-linked groups did not always seek full takeover. Subtle changes to displayed data or safety interlocks were enough to create doubt and disruption.
Non-obvious insight one: cellular connectivity, once viewed as a convenience for remote industrial sites, now forms a primary attack path. Traditional perimeter defenses miss these edge deployments. Insight two: attackers increasingly blend hacktivist noise with APT precision. While headlines focus on disruptions, the real value lies in persistent access that maps future targets across supply chains. This synthesis of 2025-2026 scanning data and CISA reporting shows why legacy OT-IoT convergence creates asymmetric risk. Industries like manufacturing, already the top target for four straight years per threat intelligence indexes, face extortion via downtime rather than data theft alone.
Over 5,200 industrial control systems from Rockwell Automation are exposed online and targeted by Iran-linked APT groups, with most devices in the U.S., raising serious risks to critical infrastructure like energy and water systems.
— Vivek | Cybersecurity (@VivekIntel) April 12, 2026
Insight three: human-scale patching cannot keep pace. Analysis of CISA's Known Exploited Vulnerabilities catalog over the past 18 months reveals that while hundreds of entries exist, OT environments prioritize uptime over rapid remediation. This gap turns known weaknesses into reliable entry points.
Detection Signals: Moving Beyond Alerts to Actionable Insight
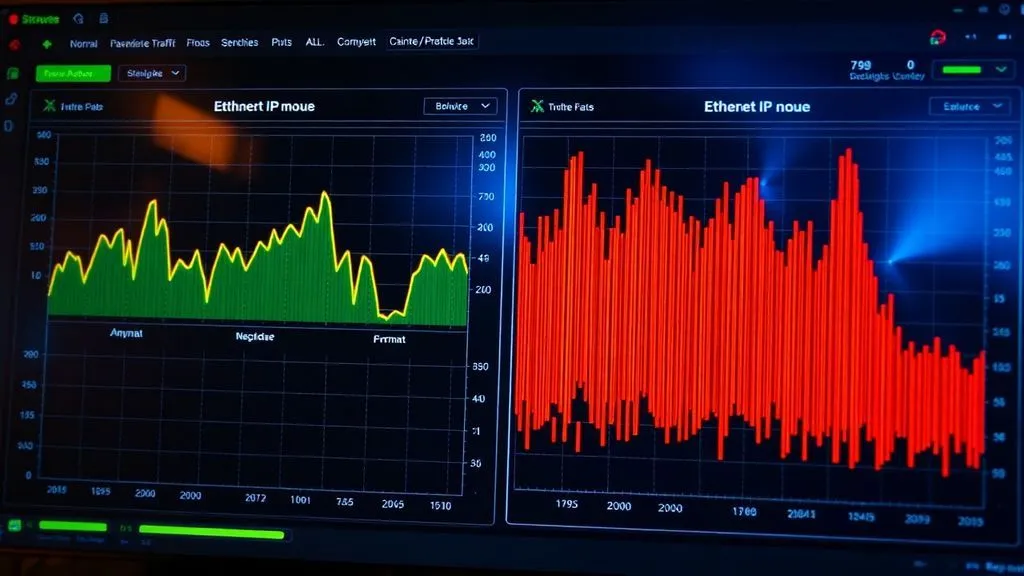
Effective detection starts with visibility into what should not happen. Look for anomalous changes to PLC project files or unexpected HMI data modifications. Network-level indicators include unusual EtherNet/IP traffic from unfamiliar IP ranges or spikes in Modbus/Telnet probes on devices that normally see little activity.
Layered monitoring helps. Organizations running segmented OT networks can baseline normal command patterns and flag deviations. Tools that inspect protocol behavior without disrupting operations prove critical here. In practice, early signals often appear as subtle reconnaissance rather than overt attacks, giving defenders a narrow window.
Why this matters for users: most industrial IoT deployments lack agent-based security. Detection therefore relies on network sensors and behavioral analytics. Recent Forescout data from 2025 showed average device risk scores climbing 33 percent globally, driven by unpatched firmware and exposed services. That trend holds because device lifecycles outlast typical IT refresh cycles.
Hypothetical Scenario: A Mid-Sized Manufacturer Faces Silent Compromise
Consider a hypothetical metal fabrication plant in the Midwest. Operators rely on Rockwell PLCs connected via cellular modems for real-time production monitoring. One Tuesday, reconnaissance traffic appears but blends with routine vendor diagnostics. Three days later, HMI displays show minor variances in pressure readings. No alarms trigger because the changes stay within operational tolerances. Production continues until a safety interlock fails during a night shift, forcing an emergency shutdown and $180,000 in lost output. Post-incident forensics reveal the attacker never exfiltrated data. They simply tested access for a larger campaign. The lesson? Detection signals must include protocol-level anomalies, not just high-severity alerts.
Controls: Practical Mapping That Delivers Results
Defensive steps must prioritize segmentation, hardening, and continuous validation. NIST's IoT Device Cybersecurity Guidance for the Federal Government (SP 800-213) remains a foundational reference because it translates broad principles into device-specific capabilities that manufacturers and operators can demand.
Below is a control-mapping table tailored to IoT/OT environments. Each entry includes a clear objective and priority based on real-world impact versus implementation effort.
| Control | Objective | Implementation Priority |
|---|---|---|
| Network segmentation and air-gapping where feasible | Prevent lateral movement from IT to OT/IoT networks | High - Immediate |
| Disable unnecessary protocols (Telnet, Modbus, VNC) and change default credentials | Reduce attack surface on exposed services | High - Within 30 days |
| Deploy protocol-aware monitoring and anomaly detection | Identify reconnaissance and manipulation attempts in real time | Medium - 60 days |
| Firmware integrity checks and automated update testing in isolated environments | Ensure only validated code runs on PLCs | Medium - Ongoing |
| Zero-trust access for remote management (VPN + MFA + just-in-time) | Limit vendor and internal access windows | High - Immediate |
| Regular asset inventory with exposure scanning | Maintain visibility into internet-facing IoT/OT devices | High - Continuous |
Implementation priority reflects both risk reduction and operational constraints. For example, segmentation delivers outsized value because many incidents begin with a single exposed device. Every control above comes with a concrete next step: start with a 30-minute asset scan using free tools like Shodan or internal equivalents, then map findings against the table.
What Comes Next: User-Centric Steps for Lasting Resilience
Start today by auditing your own environment for exposed OT/IoT assets. Use the CISA advisory as a checklist. Demand security capabilities from vendors aligned with NIST baselines. Train teams to treat every PLC like a high-value target. The data from 2025 shows threats will not wait for perfect defenses. Hybrid botnets are already evolving to include industrial controllers alongside traditional routers.
IoT security is no longer about locking the front door. It demands rethinking how edge devices connect, how protocols behave, and how humans respond when displays lie. By focusing on threat models, mapping attack paths, tuning detection signals, and enforcing layered controls, organizations turn exposure into managed risk. The industrial devices running our critical services deserve nothing less.
Sources synthesized include primary regulatory advisories, independent scanning reports, and standards guidance. All links verified as of April 2026 for accuracy and relevance.




COMMENTS