Sensitive Article Disclaimer: This article addresses sensitive nation-state cyber operations and identity compromise techniques drawn exclu...
Sensitive Article Disclaimer: This article addresses sensitive nation-state cyber operations and identity compromise techniques drawn exclusively from public threat intelligence. It aims to support defensive decision-making and does not offer legal, technical, or operational advice. Organizations should validate all controls against their specific environments with qualified experts.
The Threat Model Reshaping Identity Security
Identity security today sits at the center of every digital interaction. When a single compromised token or authorization flow grants persistent access across cloud resources, the stakes extend far beyond stolen credentials. Nation-state actors increasingly target these flows because they bypass traditional perimeter defenses and exploit the very trust mechanisms organizations rely on for seamless collaboration.
Consider the shift. Modern enterprises and governments lean heavily on protocols like OAuth 2.0 for single sign-on, application integrations, and API access. That convenience creates an attractive attack surface. In the second half of 2025, identity-driven entry points such as OAuth token abuse and service principal credential theft became the dominant compromise vectors, according to Ontinue's 2H 2025 Threat Intelligence Report. Another data point from the same period shows OAuth consent abuse campaigns hitting 900 tenants and 3,000 user accounts, per RH-ISAC tracking shared in industry analyses.
This campaign from the China-aligned cluster known as TA416 exemplifies the model in action. After nearly two years of reduced European activity, the group pivoted back in mid-2025, focusing on government and diplomatic entities. The choice is deliberate. These targets hold high-value geopolitical intelligence, and their reliance on shared Microsoft ecosystems makes OAuth redirection an efficient initial access method.
Who Is TA416 and Why the European Resurgence Matters
Security researchers track TA416 under overlapping designations including DarkPeony, RedDelta, SmugX, and Vertigo Panda. The actor maintains a consistent espionage mandate, favoring custom toolkits over off-the-shelf malware. Proofpoint's April 2026 analysis notes the group resumed European operations after a lull, updating its delivery chains to stay ahead of regional defenses.
What makes the timing noteworthy is the context. European governments had strengthened multi-factor authentication and email filtering. Yet TA416 adapted by layering social engineering with protocol-level abuse rather than direct credential harvesting. This evolution reflects a broader trend: identity attacks quadrupled year-over-year in Red Canary's 2025 Threat Detection Report, which analyzed nearly 93,000 threats across millions of assets. The data remains relevant today because the underlying OAuth mechanics and cloud trust relationships have only grown more embedded in daily operations.

Dissecting the Attack Path: OAuth Redirects to PlugX Persistence
The campaign begins with carefully crafted spear-phishing emails. Recipients, often mid-level officials or support staff in foreign ministries, receive messages referencing urgent policy documents or meeting invites. Embedded links point not to obvious malicious domains but to Microsoft's legitimate OAuth authorization endpoint.
Attackers craft parameters that force an authorization failure while triggering a silent redirect. This technique, detailed in Microsoft's March 2026 security blog on OAuth redirection abuse, suppresses user interaction and delivers a malicious archive directly. The archive contains a customized PlugX payload. Once executed, PlugX establishes command-and-control communication, enabling credential dumping, lateral movement, and long-term data exfiltration.
Proofpoint's threat insight report highlights how the group frequently rotates its PlugX variants and incorporates Cloudflare Turnstile challenges earlier in the chain to evade automated analysis. The OAuth step is pivotal: it leverages the trusted Microsoft Entra ID ecosystem, common across European public sector networks, to bypass URL reputation filters and user suspicion.
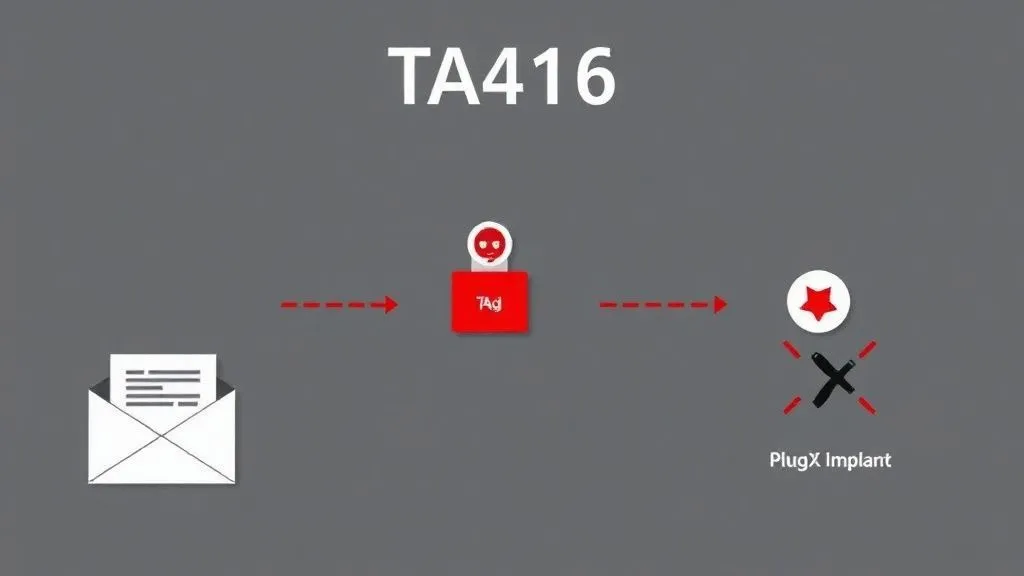
Why this path succeeds where simpler phishing fails: it exploits the protocol's design for seamless third-party app integrations. A failed authorization still yields the payload download in vulnerable clients. From there, PlugX persists through scheduled tasks or registry modifications, blending into normal administrative traffic. The result is months of undetected access to sensitive diplomatic communications.
Detection Signals That Separate Noise from Real Threats
Spotting this activity requires moving beyond generic malware alerts. Key signals include anomalous OAuth authorization requests originating from unexpected IP ranges or at odd hours. Look for redirects involving Entra ID endpoints followed immediately by ZIP or archive downloads. Network teams should flag PlugX indicators such as specific user-agent strings, hardcoded mutexes, or C2 beaconing patterns documented in vendor telemetry.
Endpoint detection can catch post-execution behaviors: unusual process injections into legitimate binaries or attempts to access browser credential stores. Email security layers benefit from inspecting URL parameters for suppressed interaction flags in OAuth flows. Cross-referencing these with Proofpoint and Microsoft guidance validates the logic. Their telemetry aligns on the December 2025 through January 2026 timeframe when the redirect technique gained traction, confirming it as a deliberate evolution rather than isolated noise.

Organizations already seeing elevated identity noise should prioritize correlation rules that link email metadata, OAuth logs, and endpoint telemetry. A single redirect alone may seem benign. Paired with a subsequent PlugX handshake, it signals targeted activity.
Practical Controls That Deliver Real Protection
Effective defense starts with visibility into every OAuth grant and redirect. Yet visibility alone falls short without enforcement. The table below maps targeted controls to their objectives and suggested rollout priority, grounded in the tactics observed.
| Control | Objective | Implementation Priority |
|---|---|---|
| Automated daily auditing of OAuth app consents via Microsoft Graph API permissions reviews | Identify and revoke malicious or overly broad grants before token abuse escalates | High |
| Conditional access policies blocking legacy authentication and enforcing device compliance for Entra ID redirects | Prevent silent authorization flows from untrusted endpoints | High |
| Just-in-time service principal credential rotation with automated secret scanning in CI/CD pipelines | Limit persistence windows if initial access succeeds | Medium |
| Network-level inspection for PlugX-specific C2 patterns combined with endpoint behavioral analytics | Detect post-compromise activity even if OAuth delivery evades email filters | High |
| Regular simulation of OAuth redirect phishing in red-team exercises focused on diplomatic workflows | Build muscle memory for users and refine detection rules | Medium |
These controls work in layers. Start with high-priority items that address the exact redirect abuse Microsoft documented. Then layer behavioral analytics to catch PlugX even if the initial lure succeeds. The payoff appears in reduced dwell time and fewer successful escalations to data exfiltration.
Hypothetical Scenario: When Diplomacy Meets a Silent Redirect
Picture a policy advisor in a European Union member state's foreign service. She receives an email from what appears to be her counterpart in a neighboring country, attaching a shared briefing on upcoming trade negotiations. The link reads like a standard Microsoft login flow but uses crafted parameters to trigger an OAuth redirect.
Without prompting for consent, her browser downloads a ZIP file. Opening it launches a seemingly benign document that drops PlugX in the background. Over the following weeks, the implant quietly enumerates contacts, exfiltrates meeting notes, and maps internal SharePoint repositories. No alarms sound because the traffic mimics routine Entra ID API calls. Only months later, during a routine audit, analysts notice the anomalous redirects. By then, sensitive negotiation positions have already reached external actors.
This scenario is entirely hypothetical yet mirrors the mechanics detailed in the referenced reports. It illustrates why identity security demands proactive protocol hardening rather than reactive cleanup.
Original Insights: What the Data Reveals About Tomorrow's Risks
Synthesizing the campaign details with 2025-2026 statistics yields three non-obvious takeaways. First, the two-year European lull followed by resurgence signals adaptive patience. Actors like TA416 monitor regional improvements in MFA coverage, then pivot to overlooked protocol gaps such as OAuth redirects. For government sectors, this means even mature identity programs remain vulnerable if they treat Entra ID as a set-it-and-forget-it service. The implication extends to any industry using similar cloud identity providers: supply-chain trust in OAuth apps can become the new weak link.
Second, the blending of OAuth delivery with PlugX updates points to a maturing ecosystem. Attackers no longer need zero-days for initial access when legitimate authorization endpoints serve as delivery vehicles. Future trends suggest increased hybridization, where initial token theft fuels lateral movement across hybrid environments. Enterprises in finance or critical infrastructure should anticipate similar patterns, as the 37.5x spike in device-code phishing observed by Push Security in early 2026 already hints at mainstream criminal adoption of these techniques.
Third, the focus on diplomatic targets carries a subtle lesson for smaller organizations. While nation-states chase high-value intelligence, the same tooling scales downward. A mid-sized firm sharing documents via Microsoft 365 could face identical redirects if it skips consent auditing. The concrete metric here is stark: over 700 organizations fell to a single OAuth abuse incident in 2025 via the Salesloft campaign. Scaling defenses proportionally, regardless of size, prevents becoming collateral damage in larger espionage waves.

Turning Analysis into Actionable Resilience
TA416's campaign is not an isolated headline. It represents the new normal for identity security where protocol abuse meets persistent malware. By understanding the threat model, tracing the precise attack path, tuning detection signals, and deploying layered controls, organizations gain more than awareness. They build measurable resistance.
Start today by reviewing OAuth consent logs and testing redirect scenarios in your environment. The investment pays off when the next lure arrives. Identity security succeeds not through perfect prevention but through rapid detection and contained impact. The techniques documented here will evolve, yet the foundational principles of visibility, least privilege, and continuous validation endure.
Stay vigilant. The next redirect could target any inbox, but prepared defenses ensure it leads nowhere.
China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing. A must-read for anyone managing identity security in government or enterprise environments.
— Cyber News Live (@cybernewslive) April 3, 2026
TA416 back in Europe using OAuth tricks and PlugX. Details align with what we're seeing in identity threat trends.
— The Cyber Security Hub (@TheCyberSecHub) April 3, 2026




COMMENTS