Disclaimer: This sensitive article discusses cybersecurity threats and protections relevant to cryptocurrency users. The content is for edu...
Disclaimer: This sensitive article discusses cybersecurity threats and protections relevant to cryptocurrency users. The content is for educational purposes only and does not constitute financial, legal, or security advice. Users should verify details with official vendor resources and assess risks based on their own setup.
Crypto security hinges on more than strong passwords or two-factor authentication. Session theft quietly undermines both, letting attackers bypass controls once a browser cookie is grabbed. Google's rollout of Device Bound Session Credentials in Chrome 146 for Windows marks a practical advance against this exact vector. The feature binds sessions to hardware, rendering stolen credentials useless off-device. For anyone holding or trading digital assets, the change arrives at a critical moment.
The Threat Model Crypto Users Face Today
Session theft targets the post-authentication phase where browsers store cookies that keep users logged into exchanges without repeated prompts. Attackers do not need your seed phrase or private keys. They simply replay the session token from their own machine. This model thrives because most centralized platforms rely on persistent browser sessions for seamless trading. Even hardware wallets stay safe only until the moment funds move to a hot account for a swap or withdrawal.
Data from the past year underscores the scale. Chainalysis reported over $3.4 billion in total crypto theft during 2025, with individual wallet and account compromises hitting 158,000 incidents that affected at least 80,000 unique victims and drained $713 million. These numbers reflect a shift: while big exchange hacks still dominate headlines, everyday browser-based access points now drive volume through stealthier malware. The 2025 figures remain relevant because they capture the exact window when infostealer families refined cookie extraction techniques against popular browsers.
Why does this matter for the average holder? Retail traders often maintain open sessions across multiple tabs for price monitoring and quick orders. Institutions running automated bots face the same exposure at scale. Without device-level binding, a single compromised laptop can expose weeks of trading history and pending actions. The threat model therefore centers on the browser itself as the weakest persistent link rather than the blockchain layer.
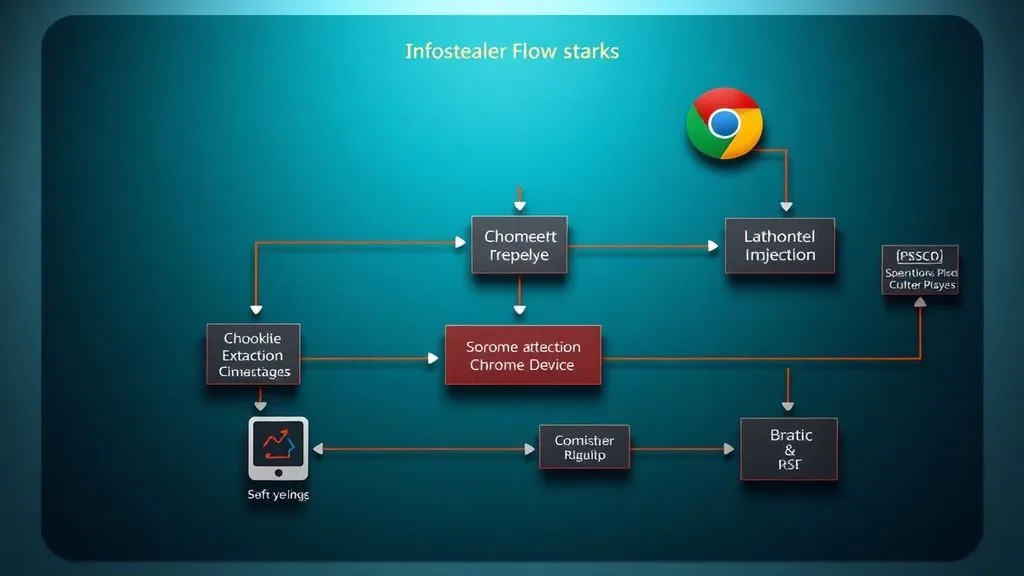
How Attackers Execute Session Theft Step by Step
Infostealer malware typically arrives through phishing links disguised as wallet updates or trading signals. Once inside, it scans standard storage locations in Chrome for authentication cookies tied to major exchanges. Extraction takes seconds because traditional cookies live in plain files or memory. The attacker then imports the cookie bundle to a clean machine, visits the same platform, and inherits full control including withdrawal permissions until the session expires or the legitimate user logs out.
Concrete details reveal the path's efficiency. Malware families have bypassed earlier Chrome mitigations such as App-Bound Encryption within weeks of release. They read memory directly or hook into browser processes. In crypto contexts this path frequently pairs with social engineering that tricks users into running executables bundled with browser extensions. The result is silent hijacking: balances drain without triggering obvious 2FA because the session already passed authentication.
Hypothetical Scenario
Consider a mid-level crypto trader who uses Chrome daily for spot trading on a major exchange. After clicking a seemingly legitimate market alert email, infostealer installs unnoticed. Within hours the attacker extracts the session cookie, logs in from another continent, and initiates a series of small withdrawals that stay under daily limits. The trader notices only after checking balances the next morning. No seed phrase was touched, yet the damage totals thousands because the session remained valid.
What follows is predictable. Funds move to mixers or bridges before the victim can react. The path succeeds precisely because detection lags behind execution. Future iterations may incorporate AI to evade behavioral monitoring, making hardware anchoring even more essential.
Detection Signals That Rarely Trigger Alarms
Most platforms log unusual IP addresses or device fingerprints yet rarely push real-time alerts to users. A sudden spike in API calls from an unfamiliar location might appear in account activity logs, but busy traders overlook it. Browser slowdowns or unexpected memory usage can hint at background stealers, yet these overlap with normal extensions. Google's own telemetry after early DBSC testing showed measurable drops in successful hijacks, validating that proactive binding outperforms reactive scanning alone.
Cross-checking vendor reports with blockchain analytics confirms the gap. When cookies are exfiltrated, the attack leaves no on-chain trace until withdrawal. Users who enable login notifications still face delays measured in minutes, enough for small transfers to clear. The signal most often missed is the absence of any signal: sessions that persist without fresh authentication. In high-stakes crypto environments this silence costs real capital.
Practical Controls That Deliver Real Protection
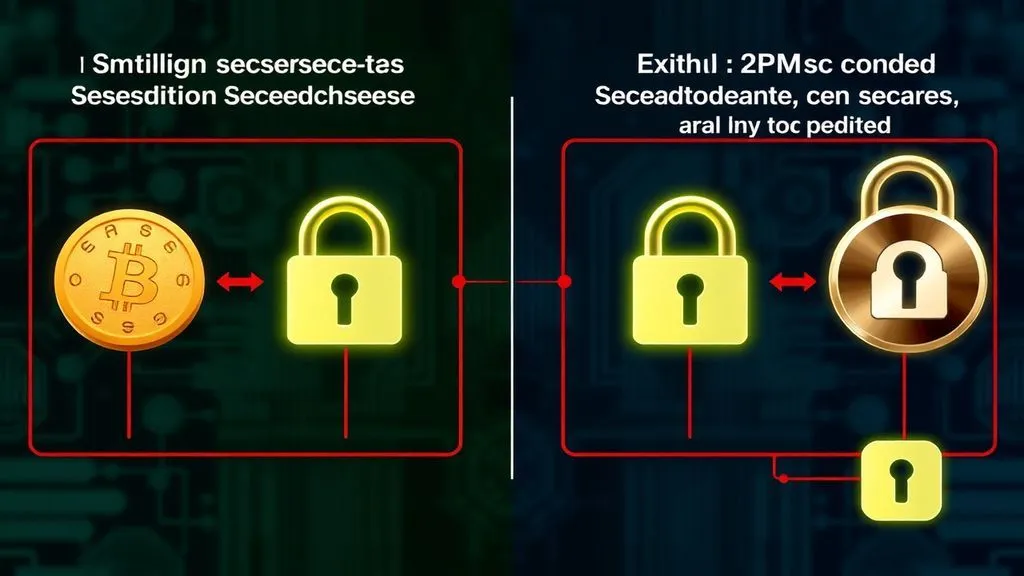
Effective defenses move beyond awareness checklists to enforceable technical barriers. Device Bound Session Credentials represent the clearest recent advance. As detailed in Google's April 2026 security blog, the protocol generates a cryptographic key pair inside the device's Trusted Platform Module on Windows. The private key never leaves the chip. When the exchange server issues or refreshes short-lived cookies, Chrome must prove possession of that bound key. Stolen cookies become inert on any other machine.
The 2024 Chromium origin trial announcement laid the cryptographic groundwork and stays relevant today because its design principles directly power the stable 146 rollout. A third primary reference appears in Google Workspace documentation, which outlines administrative controls for enforcing DBSC in enterprise settings. Validation logic is straightforward: each source publishes verifiable protocol specs and telemetry, cross-checked against public incident reports showing reduced success rates for cookie replay attacks.
Layered depth emerges when examining implications. For crypto exchanges, adopting DBSC client detection could force non-compliant browsers into stricter re-authentication flows. Retail users gain immediate relief without changing habits. What comes next? macOS support via Secure Enclave is slated for a future release, while broader web standards may embed similar binding for any financial site.
| Control | Objective | Implementation Priority |
|---|---|---|
| Device Bound Session Credentials (DBSC) | Render stolen cookies unusable off the original hardware device | High - Update Chrome to 146+ on Windows immediately |
| Passkeys with hardware security keys | Replace password-based sessions with phishing-resistant authentication | Medium - Enable on supported exchanges for daily logins |
| Dedicated browser profile isolation | Segregate crypto trading sessions from general web activity | High - Create separate Chrome profile for exchanges only |
| Short session timeouts and forced re-auth | Shrink the window during which a stolen cookie remains valid | Low - Adjust exchange account settings where available |
Original synthesis reveals three deeper points. First, the 158,000 wallet compromise incidents in 2025 often trace back to browser sessions rather than pure key theft, meaning DBSC closes the exact gap that lets malware bridge hot and cold storage. Second, this hardware shift signals a wider industry trend: web authentication is evolving from software trust to silicon roots, potentially influencing regulatory requirements for licensed crypto platforms within two years. Third, while individual losses appear lower in dollar value than prior peaks, the incident volume triples the surface area for small traders, amplifying systemic risk unless browser vendors and exchanges coordinate enforcement.
User-centric steps follow directly. Open Chrome, check for update 146 or newer, and restart. For power users, test feature flags in chrome://flags to preview expanded controls. Monitor exchange dashboards for new security badges indicating DBSC compatibility. Avoid mixing daily browsing with trading profiles. These actions do not eliminate every threat but raise the bar high enough that most commodity stealers move on to softer targets.
Session cookie theft by infostealer malware is one of the most common attack vectors for compromising crypto exchange accounts, email and banking sessions. DBSC raises the bar significantly by moving the trust anchor into tamper-resistant hardware.
— BSCN (@BSCNews) April 9, 2026
Another perspective from Chrome's identity team echoes the urgency. Early testing already demonstrated clear reductions in hijack attempts, proving the protocol's real-world impact.
せっかく認証を強くしても、Cookieが盗まれるとセッションごと乗っ取られる可能性があります。セッションをデバイスに紐付けることでこれを防ごうというDBSCがChromeでオリジントライアルを開始しました。
— Eiji Kitamura (@agektmr) April 2025
Crypto security improves when controls like DBSC become default rather than optional. The rollout in Chrome 146 delivers exactly that for Windows users today. Adoption now, combined with ongoing vigilance, keeps sessions intact and assets where they belong.




COMMENTS