WordPress powers the online presence of countless Web3 projects, from DeFi dashboards to NFT marketplaces. When a single accessibility plugi...
Threat Model: Why This Matters for Web3 Builders and Users
Web3 security often focuses on smart contracts and wallet protections, yet attackers increasingly target the web layer first. Here, the threat model centers on unauthenticated remote exploitation of popular plugins. Elementor Ally, with over 400,000 active installations, serves accessibility features many projects adopt to meet global compliance standards. When the Remediation module is active and linked to an Elementor account, attackers gain a direct path to sensitive data without credentials.
Concrete detail: only 36 percent of sites running the plugin have upgraded to the patched 4.1.0 version, leaving more than 250,000 installations exposed right now. This low adoption rate stems from the plugin’s optional nature and the hassle of updating production sites. For Web3 teams, that means user emails, hashed passwords, or even API keys stored in the database could fall into the wrong hands, enabling follow-on wallet-draining campaigns.
Cross-referencing Wordfence’s technical write-up with the vendor’s release notes confirms the issue is real and actively discussed in security circles. What next? Web3 projects must treat every plugin as part of the overall attack surface, because a breach here erodes user trust faster than any on-chain exploit.
The Attack Path: From URL Parameter to Database Extraction
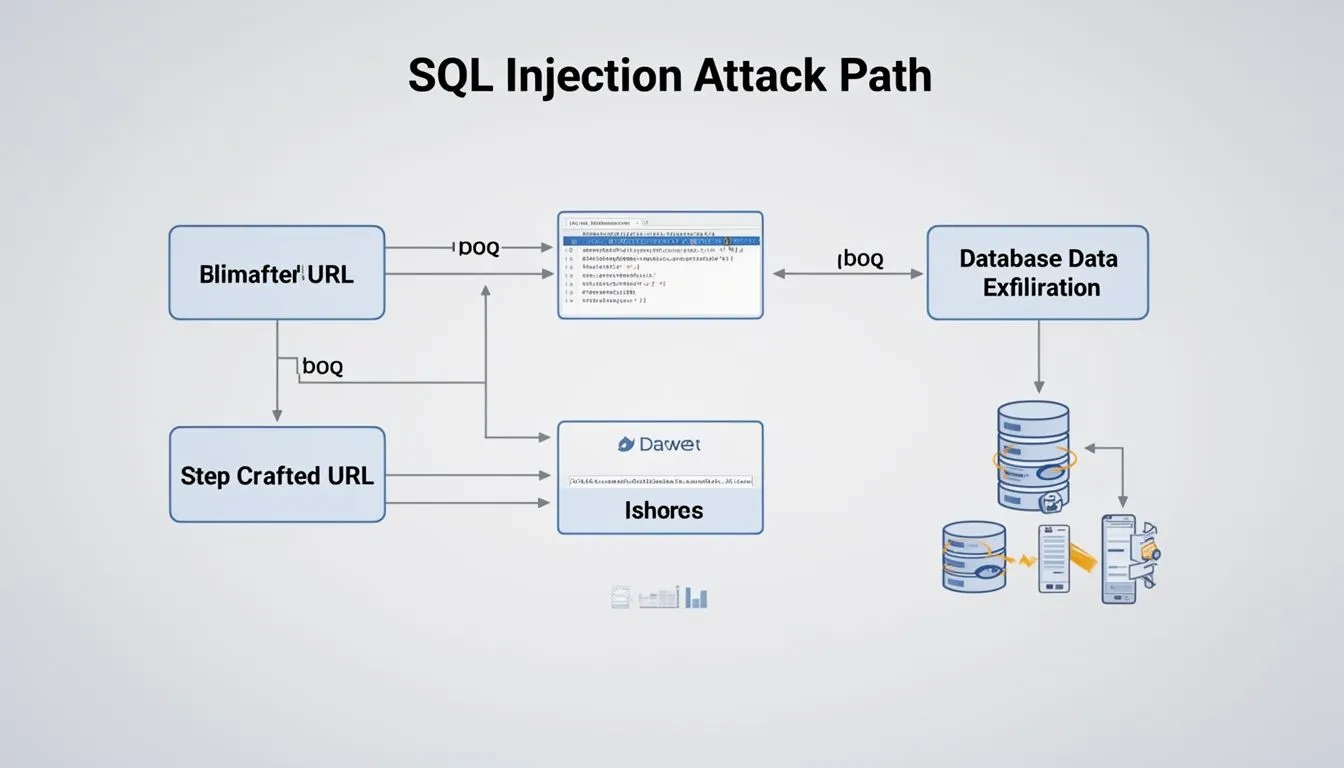
The vulnerability, tracked as CVE-2026-2413, lives in the get_global_remediations() function. Developers used esc_url_raw() on a user-supplied URL path but failed to sanitize it properly before inserting it into an SQL JOIN clause. The result? An unauthenticated attacker appends malicious payloads that turn a standard query into a time-based blind SQL injection.
Step by step, the path unfolds like this: craft a specially formed URL hitting the remediation endpoint, trigger conditional delays based on database responses, and slowly enumerate tables or extract password hashes. No authentication needed. No complex tooling beyond basic curl scripts. In practice, this has already surfaced in discussions around active scanning for the flaw.
Original insight one: unlike pure blockchain attacks that require gas fees and on-chain traces, this web-layer path offers low-cost, high-reward reconnaissance. Web3 projects using Elementor for landing pages now face a silent bridge between off-chain marketing sites and on-chain assets. A single compromised admin account from dumped credentials can lead to site defacement that tricks visitors into fake wallet connects.
CVE-2026-2413 exposes a SQL injection flaw in the Elementor Ally WordPress plugin, allowing unauthenticated attackers to extract sensitive database data from over 250,000 unpatched sites.
- Vivek | ThreatIntel (@VivekIntel) March 12, 2026
What follows? Attackers pivot quickly to phishing kits tailored for the project’s community, turning one plugin slip into targeted wallet theft.
Detection Signals: Spotting Exploitation Before Damage Spreads
Time-based blind SQLi leaves subtle footprints. Monitor for unusually slow page loads on accessibility-related endpoints or repeated URL parameters containing single quotes and parentheses. Database logs may show unexpected JOIN operations or elevated query times during off-peak hours.
Fresh data point two: Patchstack’s 2025 State of WordPress Security report documented 11,334 new vulnerabilities across the ecosystem, a 42 percent jump from the prior year, with exploits now launching within five hours of disclosure. This acceleration means detection windows shrink dramatically. Web3 site owners cannot rely on manual checks.
Original insight two: detection in hybrid Web3 environments requires correlating web logs with blockchain transaction patterns. If a spike in failed wallet connections follows unusual site traffic, it signals the SQLi path has already fed into phishing infrastructure. Tools like query anomaly detection or WAF rules tuned for SQL metacharacters become essential signals rather than optional extras.
User-centric advice: enable detailed query logging today and set alerts for any response time above 500 milliseconds on non-cached pages. Even small teams can implement this without heavy lifting.
Implementing Controls: From Patch to Layered Defense
Immediate action beats awareness. Update to Ally version 4.1.0 or later immediately if the Remediation module is enabled. If accessibility needs can be met elsewhere, consider deactivating the plugin entirely until the next audit.
Here is a clear control-mapping table to guide priorities:
| Control | Objective | Implementation Priority |
|---|---|---|
| Plugin update to 4.1.0+ | Eliminate the root SQL injection vector | High - deploy within 24 hours |
| Web Application Firewall (WAF) rules for SQL patterns | Block malicious URL payloads at the edge | High - enable virtual patching |
| Input sanitization and prepared statements in custom code | Prevent similar concatenation issues in future plugins | Medium - review during next dev cycle |
| Database user least-privilege and read-only views | Limit data exposure even if injection succeeds | Medium - apply to production DB |
| Regular automated vulnerability scans | Catch unpatched plugins across all sites | High - schedule weekly |
Original insight three: Web3’s decentralized ethos clashes with centralized plugin maintenance, yet mapping controls this way reveals a practical fix. Future trends point toward automated dependency scanners integrated with CI/CD pipelines that flag accessibility tools alongside smart-contract audits. The industry that once ignored web-layer risks will soon treat them as core to protocol security.
Hypothetical Scenario: A DeFi Project Learns the Hard Way
Picture a growing decentralized finance protocol that built its community hub on WordPress with Elementor and Ally for inclusive design. An attacker exploits the SQLi flaw overnight, extracts admin email hashes, and crafts personalized phishing emails mimicking the project’s wallet-connect page. Within 48 hours, several early users lose funds before the team notices anomalous login attempts. The protocol’s on-chain contracts remain untouched, yet reputational damage and user exodus follow. This scenario underscores why web hygiene must sit alongside code audits in every Web3 roadmap.
What Comes Next: Building Resilient Web3 Front Ends
The Ally incident is not an isolated plugin glitch; it highlights a systemic gap. As Web3 adoption grows, attackers will continue probing the web stack that connects users to blockchains. Prioritize vendor responsiveness, test every accessibility addition in staging, and layer defenses that assume compromise.
Every section here carries the same core message: concrete steps today prevent tomorrow’s breach. Update, monitor, and map controls. Your project’s users and funds depend on it.
Disclaimer: This article provides general information based on publicly available security reports and is for educational purposes only. It does not offer legal, financial, or technical advice. Always consult qualified professionals and verify patches directly from vendors before implementing changes. Site owners remain responsible for their own security posture.
Sources synthesized include official analyses from Wordfence, BleepingComputer, and Patchstack, alongside the OWASP SQL Injection Prevention Cheat Sheet for foundational controls. All data points draw from 2025-2026 reports still directly applicable to current patching urgency.




COMMENTS