In the evolving landscape of cybersecurity threats, a new phishing-as-a-service (PhaaS) tool called Starkiller is making waves by proxying l...
In the evolving landscape of cybersecurity threats, a new phishing-as-a-service (PhaaS) tool called Starkiller is making waves by proxying legitimate login pages to steal credentials and bypass multi-factor authentication (MFA).
This sophisticated platform allows cybercriminals to impersonate trusted brands like Apple, Google, and Microsoft, capturing user inputs in real time without raising typical red flags.
This analysis dives deep into Starkiller's mechanics, impacts, and defenses, focusing on its relevance to cybersecurity and financial sectors where account takeovers can lead to massive losses.
What is the Starkiller Phishing Service?
Starkiller is a commercial-grade PhaaS offering sold by a group known as Jinkusu, designed to facilitate large-scale identity theft.
Unlike traditional phishing kits that use static HTML copies of login pages, Starkiller dynamically loads the actual website of the targeted brand.
This approach evades detection by security tools that flag mismatched domains or suspicious code patterns.
The service operates on a subscription model, similar to legitimate SaaS products, lowering the barrier for entry-level attackers.
It supports impersonation of major platforms, including those in finance and crypto, where compromised accounts can result in unauthorized transactions or wallet drains.
Researchers from Abnormal AI first detailed Starkiller's capabilities, highlighting its rapid adoption in underground forums.
Starkiller's emergence in early 2026 underscores a shift toward more advanced adversary-in-the-middle (AitM) attacks.
By relaying traffic between victims and real sites, it captures not just passwords but also MFA tokens and session cookies for immediate account hijacks.
This makes it particularly dangerous for users in crypto trading or online banking, where real-time access can lead to swift financial exploitation.
How Starkiller Works: A Technical Breakdown
At its core, Starkiller uses Docker containers to run a headless Chrome browser instance, which loads the genuine login page of the impersonated brand.
When a victim clicks a phishing link, the tool acts as a reverse proxy, forwarding inputs like usernames, passwords, and MFA codes to the legitimate site while recording them.
Responses from the real site are then proxied back to the victim, maintaining the illusion of a normal login process.
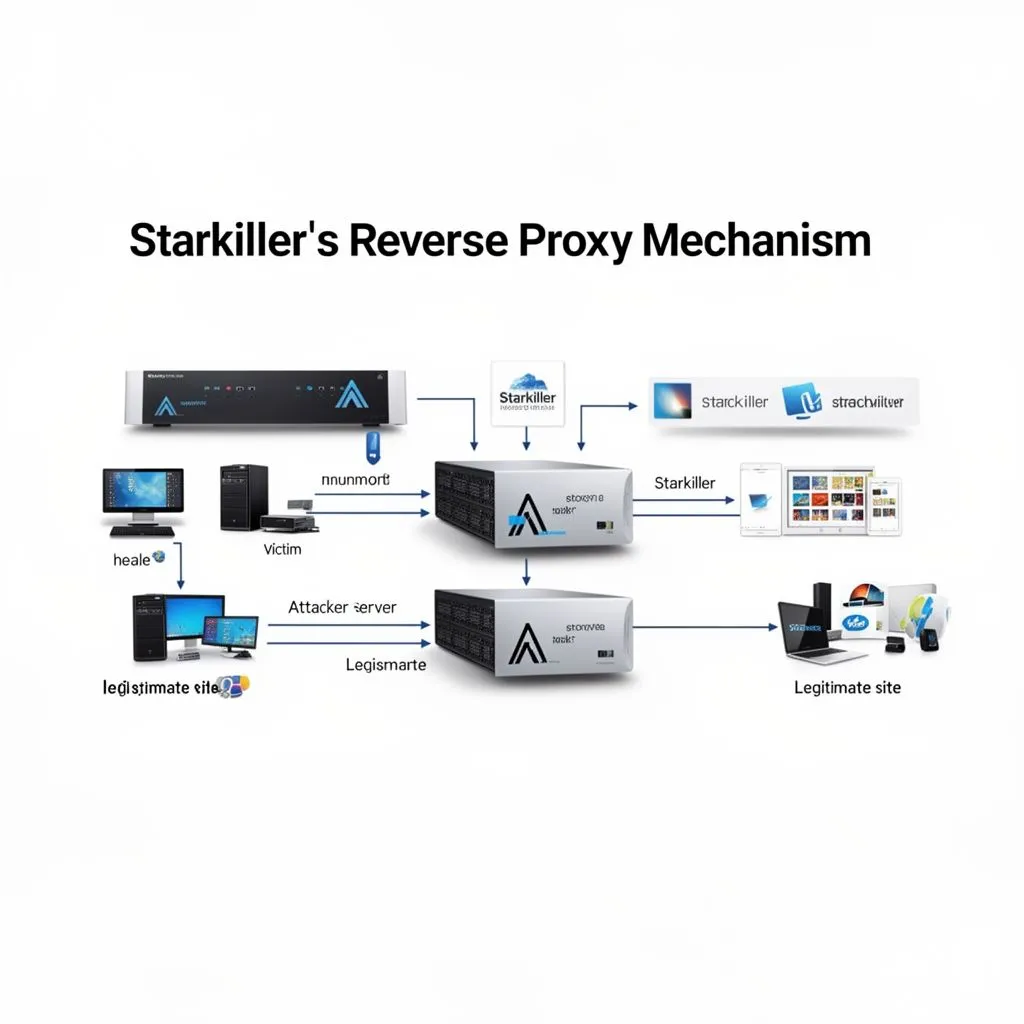
Attackers customize campaigns via a user-friendly control panel, selecting brands and generating obfuscated URLs that mimic legitimate domains using techniques like lookalike characters or "@" tricks. For instance, a link might appear as "[email protected]," fooling quick glances.
This setup bypasses MFA because the proxy captures the authentication token post-verification, allowing instant session hijacking.
In finance and crypto contexts, Starkiller can target exchange logins or wallet apps, where MFA is common but not foolproof against AitM.
The tool's ability to handle dynamic content ensures it works even with sites that use JavaScript-heavy interfaces.
Security experts note that traditional phishing defenses, like domain reputation checks, fail here since the content is pulled live from trusted sources.
The Broader Implications for Global Users
Starkiller amplifies risks in cybersecurity, especially for English-speaking global audiences reliant on cloud services and online finance.
With MFA bypass, even vigilant users can fall victim, leading to data breaches, ransomware entry points, or crypto theft.
Enterprises face heightened threats as employees' compromised personal accounts often spill over to corporate systems.
In the crypto and finance sectors, where transactions are irreversible, Starkiller enables quick drains of funds.
Reports indicate its use in targeted attacks against high-value accounts, potentially costing millions.
As phishing evolves, reliance on MFA alone is insufficient; this tool exposes gaps in current security paradigms, urging a multi-layered approach.
Global adoption of Starkiller could spike phishing success rates, claimed at 99.7% by its creators though likely exaggerated.
For English readers, awareness is key, as major brands like those in the US and UK are prime targets. This threat also intersects with regulatory pressures, like GDPR or SEC rules, where breaches from such attacks could incur hefty fines.
Practical Defenses Against Starkiller Attacks
To counter Starkiller, users should employ hardware-based MFA like YubiKeys, which are harder to proxy than app-based tokens.
Educate on scrutinizing URLs fully, avoiding clicks on unsolicited links, and using password managers that autofill only on exact domain matches.
Enterprises can deploy advanced email gateways that detect obfuscated URLs and AitM patterns.
In crypto and finance, enable transaction alerts and use cold wallets for large holdings to limit exposure.
Regular security audits and employee training on emerging threats like proxy phishing are essential.
Tools like browser extensions for URL safety checks can add another layer, though no single measure is infallible.
Monitoring for unusual login attempts and enabling account lockouts after failed MFAs helps mitigate post-compromise damage.
For global users, staying informed via trusted sources like Krebs on Security is vital. Ultimately, combining technology with user vigilance forms the strongest defense against evolving PhaaS like Starkiller.
Expert Opinions from X
Security professionals on X have been quick to discuss Starkiller's dangers. Here's a reference from a verified account sharing insights.
🚨 New “Starkiller” Phishing Kit Bypasses MFA by Proxying Real Login Sites A sophisticated phishing‑as‑a‑service platform called Starkiller uses headless browsers and reverse proxies to load genuine login pages and harvest credentials and MFA tokens in real time, lowering the technical barrier for large‑scale credential theft. This evolution in phishing infrastructure makes traditional phishing detection and MFA protections far less effective. 🕷️ Malware: Starkiller phishing kit 🎯 Target: Global/Online Platforms & Users #️⃣ Category: #CyberCrime #Malware 🔗 URL: https://t.co/7efN4HQ0TR
— ThreatSynop (@ThreatSynop) March 4, 2026
Another perspective highlights the technical sophistication.
🚨 New phishing nightmare: Starkiller Phishing Suite is here! 😈 It uses AiTM reverse proxy magic ✨ to load REAL login pages (Google, Microsoft, Apple, etc.) in headless Chrome via Docker containers. Victims enter creds + MFA codes normally → everything relayed live through attacker servers → keystrokes, tokens, sessions stolen! 🔑💥 MFA? Bypassed in real-time. Account takeover made easy. 🥷 Stay vigilant – never trust suspicious links! ⚠️🔒
— Ahmed Nawaz Khalid (@hushed_ahmie) March 4, 2026
For more on cybersecurity threats, visit Krebs on Security or explore resources from Abnormal AI.




COMMENTS