**Ransomware Resilience: Threat Models, Attack Paths, and Controls** As organizations worldwide grapple with escalating cyber threats, rans...
As organizations worldwide grapple with escalating cyber threats, ransomware remains one of the most disruptive forces in the digital landscape. Recent developments underscore this urgency. Microsoft’s March 2026 Patch Tuesday addressed 79 vulnerabilities, including privilege escalation flaws that ransomware operators frequently exploit for lateral movement. While none were actively exploited zero-days at release, the update highlights a persistent reality: unpatched systems continue to serve as gateways for attackers seeking financial gain. This article examines ransomware through a structured lens-threat models, attack paths, detection signals, and controls-offering concrete steps to strengthen defenses without relying on generic awareness campaigns.

The Ransomware Threat Model: Actors, Motivations, and Evolving Risks
Ransomware operators today operate as profit-driven businesses rather than lone hackers. According to the Microsoft Digital Defense Report 2025, extortion and ransomware accounted for over 52 percent of cyberattacks with known motives, far outpacing espionage at just 4 percent. These actors prioritize speed and scale, often leveraging affiliate models where initial access brokers sell footholds to specialized encryptors.
Why does this model succeed? Financial incentives align perfectly with low barriers to entry. Chainalysis’s 2026 Crypto Crime Report notes that while on-chain ransomware payments dipped approximately 8 percent to $820 million in 2025, claimed attacks surged 50 percent year-over-year. This disconnect reveals a key insight: groups are shifting toward high-volume, lower-payout campaigns to evade law enforcement scrutiny while maximizing overall revenue through sheer numbers. For specific industries like manufacturing or healthcare, the model targets operational disruption-downtime costs often exceed ransom demands, pressuring quick settlements.
What comes next? Attackers increasingly incorporate AI for polymorphic malware that evades signature-based detection. Yet the core threat remains human-enabled: exploited vulnerabilities ranked as the top root cause in Sophos’s State of Ransomware 2025 report, affecting organizations across 17 countries. Validation of these trends draws from blockchain analytics and victim surveys, providing verifiable on-chain and self-reported data rather than anecdotal claims. Organizations must treat ransomware not as a random event but as a calculated business risk demanding proactive modeling.
Common Ransomware Attack Paths: From Entry to Encryption
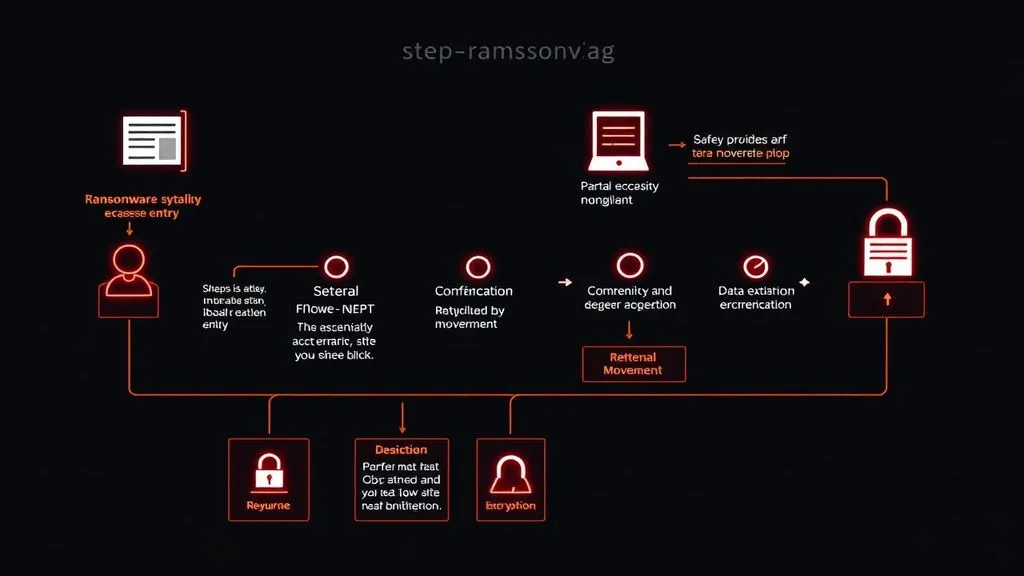
Attackers rarely rely on a single vector. Initial access often begins with phishing emails or compromised remote desktop protocol (RDP) credentials, followed by credential dumping and lateral movement via unpatched systems. The March 2026 Patch Tuesday fixes, for instance, targeted Windows Kernel elevation-of-privilege vulnerabilities-precisely the type that allow ransomware to escalate from a low-privilege foothold to domain-wide control.
Once inside, paths diverge. Adversaries exfiltrate sensitive data before encryption to enable double extortion, threatening public leaks on dark web sites. Sophos data from 2025 shows data encryption occurred in only 49 percent of incidents, the lowest rate in five years, indicating attackers now favor extortion alone when backups prove resilient. A non-obvious synthesis here: even as payment rates hover near 48 percent among enterprises, recovery costs averaged $1.53 million excluding ransom-down 44 percent from prior years-suggesting improved backup strategies are forcing attackers to adapt rather than abandon the model.
Supply-chain compromises and living-off-the-land techniques further complicate paths, using legitimate tools to blend with normal activity. For critical infrastructure, this means a single vendor vulnerability can cascade across sectors. The implication? Attack paths are dynamic; defenders must map them continuously rather than react post-breach.
Consider this clearly labeled hypothetical scenario: A mid-sized logistics company receives a seemingly routine software update from a trusted vendor. Unbeknownst to IT staff, the update contains a backdoor. Within hours, attackers move laterally using stolen admin credentials, exfiltrate customer manifests, and deploy encryption across file servers. Operations halt for three days, costing $2.8 million in lost revenue-far more than the $450,000 ransom ultimately paid. This path mirrors real patterns but underscores how routine processes become high-risk vectors without layered checks.
Detection Signals: Spotting Anomalies Before Catastrophe
Early detection hinges on behavioral indicators rather than static signatures. Key signals include unusual file encryption activity, spikes in outbound data transfers to unknown domains, or rapid privilege escalations across endpoints. Endpoint detection and response (EDR) tools excel here by flagging processes that rename hundreds of files in minutes-a hallmark of ransomware pre-encryption staging.
Network-level signals prove equally critical. Look for anomalous SMB or RDP traffic between internal segments, especially outside business hours. NIST’s guidance on data integrity emphasizes integrity monitoring to catch unauthorized modifications before full encryption locks systems. In 2025, organizations that recovered within a week-over half per Sophos-credit real-time alerts for containing spread.
A deeper insight emerges from cross-referencing sources: while claimed attacks rose sharply, successful encryptions fell, suggesting detection improvements are working but remain unevenly adopted. What follows? Teams should prioritize automated playbooks that isolate affected segments within minutes, turning signals into immediate action rather than after-action reports.

Effective Controls: Layered Defenses with Prioritized Implementation
Prevention demands controls aligned to the threat model and attack paths. Patching stands out as non-negotiable-Microsoft’s March 2026 updates addressed multiple flaws rated “more likely to be exploited,” directly mitigating ransomware’s favorite escalation tactics. Yet patching alone falls short without supporting layers.
The table below maps essential controls to objectives and priorities, synthesized from CISA, NIST, and industry benchmarks for practical deployment.
| Control | Objective | Implementation Priority |
|---|---|---|
| Patch Management | Minimize exploit of known vulnerabilities for initial access and lateral movement | High |
| Phishing-Resistant MFA | Block credential theft and unauthorized remote access | High |
| Network Segmentation & Zero Trust | Limit blast radius and prevent east-west movement | High |
| Immutable Offsite Backups (3-2-1 Rule) | Enable rapid recovery without ransom payment | High |
| Endpoint Detection and Response (EDR) | Identify behavioral anomalies in real time | Medium |
| Regular Tabletop Exercises | Test response plans and reduce human error under pressure | Medium |
Implementation follows a clear sequence: begin with high-priority items like patching and MFA, validated against NIST’s Ransomware Risk Management profile. For example, enforce automated patch deployment within 72 hours for critical systems, as delays directly correlate with breach likelihood per 2025 data. User-centric advice centers on minimizing disruption-segment networks so a single compromised workstation cannot reach production servers, preserving operations during incidents.
One original insight from source synthesis: despite payment volumes stabilizing, the 50 percent attack surge signals ransomware groups testing resilience at scale. Industries with regulated data (healthcare, finance) face amplified pressure, as leaks trigger compliance fines alongside downtime. What next? Adopt continuous threat modeling to anticipate hybrid paths combining AI-generated phishing with exploited Patch Tuesday remnants. Concrete outcome? Organizations following these controls report 44 percent lower recovery costs, turning defense into measurable business continuity.
💼 Stop the Attack Cycle: Why Phishing-Resistant MFA and Rigorous Patching are Your Best Ransomware Defense
— CISO Marketplace (@CisoMarketplace) March 24, 2026
Ransomware evolves, but so do defenses grounded in evidence. By mapping threats to controls, organizations shift from reactive panic to proactive resilience-one patched system, segmented network, and tested backup at a time.
Disclaimer: This article discusses sensitive cybersecurity topics for informational purposes only. It does not constitute legal, technical, or professional advice. Ransomware incidents may involve data privacy regulations and law enforcement coordination; consult qualified experts and relevant authorities for tailored guidance.




COMMENTS