Threat Model: Botnets Targeting Anonymity in Web3 Web3 ecosystems rely heavily on decentralized networks for transactions, smart contracts,...
Threat Model: Botnets Targeting Anonymity in Web3
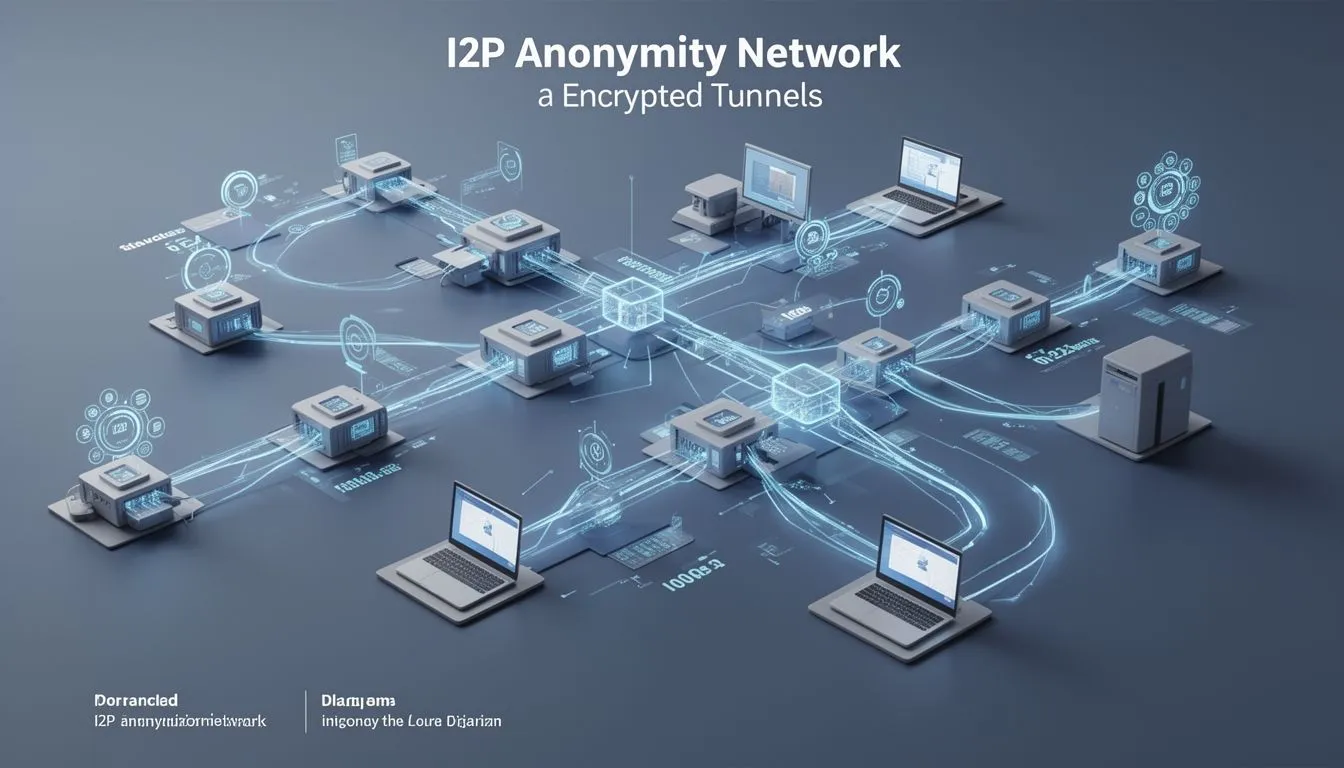
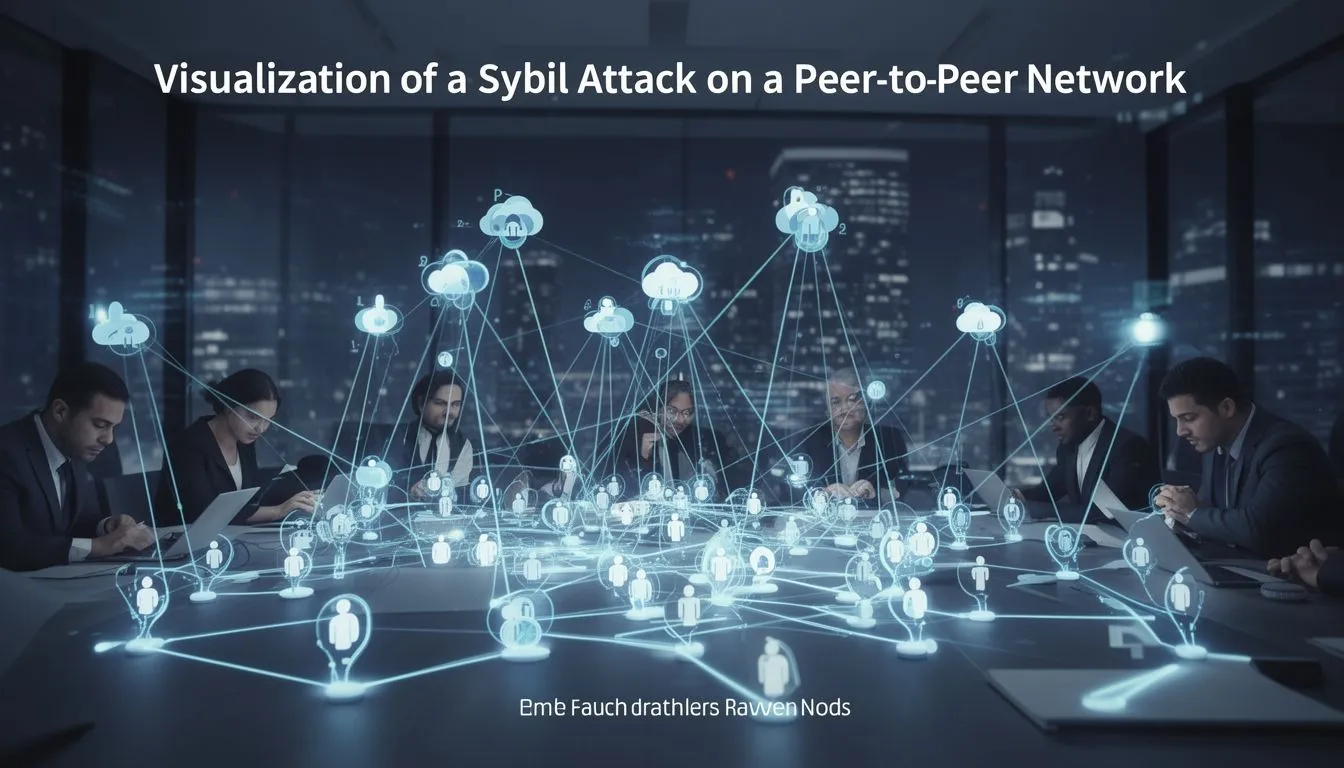
Web3 ecosystems rely heavily on decentralized networks for transactions, smart contracts, and peer-to-peer interactions. Tools like the Invisible Internet Project (I2P) provide essential anonymity by routing traffic through encrypted tunnels, shielding users from surveillance. However, botnets such as Kimwolf introduce a potent threat by overwhelming these networks, potentially exposing user identities or disrupting services. This model assumes adversaries control vast numbers of compromised devices to launch Sybil attacks, where fake nodes flood the system and degrade performance.
In Web3, where privacy is paramount for activities like cryptocurrency trading or decentralized finance (DeFi), such disruptions can lead to real-world implications. For instance, if I2P becomes unreliable, users might revert to less secure alternatives, increasing the risk of IP leaks during blockchain interactions. According to the official I2P documentation, Sybil attacks are mitigated through peer profiling, which scores nodes based on behavior to limit malicious influence.
A fresh data point from late 2025 highlights the scale: Kimwolf infected over 2 million unofficial Android TV devices, enabling massive distributed denial-of-service (DDoS) attacks peaking at 31.4 terabits per second in December.
Consider a hypothetical scenario: A Web3 startup team uses I2P to anonymously test a new DeFi protocol, routing API calls through the network to avoid competitor surveillance. Suddenly, a botnet flood like Kimwolf's causes intermittent outages, forcing the team to switch to direct connections. This exposes their IPs, allowing a rival firm to trace development activity and launch a targeted phishing campaign, resulting in stolen wallet credentials.
The Attack Path of Kimwolf on I2P
Kimwolf's operators followed a multi-stage path to disrupt I2P. Initially, the botnet spread via residential proxies, tricking services into relaying commands to vulnerable IoT devices on local networks. This bypassed traditional firewalls, infecting millions of items like streaming boxes and routers with malware that included DDoS capabilities and proxy forwarding.
By February 2026, facing takedowns of over 550 command-and-control (C2) servers, the botmasters shifted to I2P as a backup infrastructure. They attempted to integrate 700,000 infected bots as nodes, far exceeding I2P's typical 15,000-20,000 active routers. This triggered a Sybil attack, where the influx of fake identities overwhelmed routing, causing outages for legitimate users.
In a Web3 context, this path reveals vulnerabilities in anonymity tools. Cryptocurrencies like Bitcoin support I2P for peer connections to enhance privacy, but a similar flood could interrupt blockchain syncing or de-anonymize nodes in networks like Ethereum.
The botnet's ties to the earlier Aisuru network, which splintered in August 2025, add complexity. Aisuru's code was reused in Kimwolf's early versions, incorporating EtherHiding technology for blockchain-based domain resilience against takedowns.
⚠ Read this. Then read it again. Understand what it implies. Basically: A TA found a way to abuse commercial residential proxies to query your local network and attack local devices. This is a super spreading event! It bypasses NAT completely. https://krebsonsecurity.com/2026/01/the-kimwolf-botnet-is-stalking-your-local-network/
— Gi7w0rm (@Gi7w0rm) January 2, 2026
Detection Signals for Botnet Disruptions
Spotting attacks like Kimwolf's requires monitoring specific indicators. In I2P, sudden spikes in node count-such as from 20,000 to hundreds of thousands-signal a potential Sybil influx. Network latency jumps, with tunnel build success rates dropping below 80%, also flag issues, as per I2P's developer guidelines.I2P Threat Model
For Web3 users, detection extends to blockchain metrics. Unusual peer connection failures in tools like geth (Ethereum client) or irregular gossip protocol traffic could indicate botnet interference. Tools from vendors like Infoblox provide DNS telemetry to spot probing from residential proxies, a key Kimwolf tactic.
On the device level, watch for unexpected outbound traffic from IoT gadgets, often exceeding 1 Mbps per device during DDoS mobilization. Security logs from routers, following NIST guidelines for IoT security (SP 800-213), can reveal patterns like repeated failed authentication attempts.NIST IoT Security Guidelines Although published in 2021, this document stays relevant because core IoT vulnerabilities, like weak passwords, persist unchanged in modern devices.
What to know about the Aisuru-Kimwolf botnet: https://pulsedive.com/threat/Aisuru-Kimwolf - Massive botnet, 1M+ compromised devices - Kimwolf = specialized Android variant - Aisuru = parent botnet that has spawned other botnets - Used in DDoS and other attacks Expect more news and updates on this threat in the coming weeks.
— Pulsedive Threat Intelligence (@pulsedive) March 2, 2026
Implementing Controls Against Botnet Threats
To counter these risks, prioritize layered defenses. Start with device hardening: Enforce strong, unique passwords on IoT items and segment them into isolated VLANs using switches from vendors like Cisco, which recommend zero-trust models in their IoT security whitepapers.Cisco IoT Security
For I2P and Web3 integrations, enable strict peer selection in router configs, limiting connections to high-trust nodes. Regularly update software; I2P's February 2026 release (2.11.0) included enhanced flood protections.

| Control | Objective | Implementation Priority |
|---|---|---|
| Network Segmentation | Isolate IoT devices to prevent lateral movement in botnet infections | High |
| Behavioral Analytics | Detect anomalous traffic patterns indicative of Sybil attacks | Medium |
| Automated Patching | Ensure timely updates to close vulnerabilities exploited by proxies | High |
| Proxy Traffic Inspection | Block unauthorized residential proxy relays | Medium |
Deploy intrusion detection systems (IDS) tuned to I2P's garlic routing, flagging bundles exceeding normal sizes. For broader protection, integrate with standards from the Internet Engineering Task Force (IETF), such as RFC 8890 for secure IoT bootstrapping.IETF RFC 8890 Source validation here relies on cross-checking with regulatory bodies like the FCC, which endorse similar controls in their IoT labeling program launched in 2024.
Finally, conduct regular audits: Simulate Sybil scenarios using open-source tools to test resilience, ensuring Web3 operations remain uninterrupted even under botnet pressure.




COMMENTS