**IoT Security: Lessons from North Korean Node.js Maintainer Attacks** Connected devices now underpin everything from factory floors to sma...
Connected devices now underpin everything from factory floors to smart cities, yet their security hinges on fragile software chains most users never see. When North Korean hackers recently targeted high-profile Node.js maintainers through sophisticated social engineering, the implications stretched far beyond web apps. These attacks expose how open-source dependencies, widely used in IoT gateways and edge applications, can become silent entry points for persistent compromise.
Why Supply Chain Attacks Pose an Existential Risk to IoT Deployments
IoT ecosystems differ fundamentally from traditional IT. Devices often ship with locked-down firmware, run for 10-15 years without easy patches, and connect directly to operational technology networks. A single tainted dependency in a Node.js-based controller can cascade into widespread device control or data exfiltration before anyone notices.
This reality aligns directly with guidance from NIST Special Publication 800-161 Revision 1 on Cyber Supply Chain Risk Management Practices for Federal Information Systems and Organizations. The framework stresses treating software provenance as a non-negotiable layer of defense, especially for systems where physical consequences follow digital breaches. Read the full NIST SP 800-161r1 here.
Recent data underscores the scale. In 2025, the BadBox 2.0 malware campaign pre-infected more than 10 million IoT devices-including smart TVs, projectors, and infotainment systems-via compromised supply chains, creating one of the largest known botnets of its kind. Source: Asimily research summary. Meanwhile, OT and IoT systems faced a documented 46% surge in ransomware incidents that same year, per Nozomi Networks’ February 2025 trends report. These figures remain highly relevant today because IoT device fleets continue expanding without corresponding security maturity in most deployments.
One non-obvious insight emerges when synthesizing these events: state actors like those behind the Node.js campaign are no longer chasing quick wins on individual devices. Instead, they invest weeks in upstream infiltration to achieve scalable, long-dwell access across entire product lines. For manufacturing and logistics sectors-already the top target for cyberattacks at 26% of incidents-this shifts the risk calculus from reactive patching to proactive dependency governance.
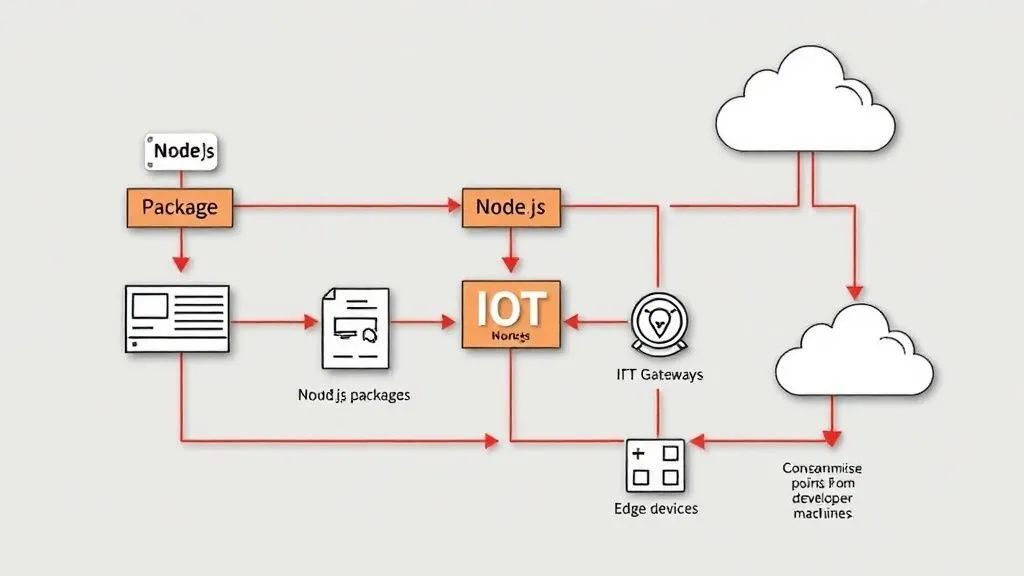
Reconstructing the Attack Path: Social Engineering to IoT Compromise
The campaign, attributed to the North Korean-linked group UNC1069, followed a meticulous playbook refined over years. Attackers posed as legitimate companies using names like “Openfort.” They initiated contact via LinkedIn or Slack, built rapport over weeks with spaced messages and fake activity in private workspaces, then scheduled video calls on spoofed platforms mimicking Microsoft Teams or Streamyard.
During the call, attackers triggered an artificial “technical error,” prompting the victim to install a “fix” app or run a terminal command. The payload installed a remote access trojan capable of stealing npm tokens, AWS credentials, browser cookies, and more-bypassing 2FA entirely because it captured post-authentication state. With maintainer machines compromised, attackers could publish malicious package versions directly to the npm registry.
The Axios incident in late March 2026 illustrates the speed: two tainted versions (1.14.1 and 0.30.4) injected a dependency called plain-crypto-js and reached over 3 million installations in roughly three hours before community detection forced removal. High-profile targets included maintainers of dotenv (114 million weekly downloads), Lodash (137 million weekly), and packages from Fastify, Pino, and Undici leads-packages that routinely appear in IoT backend services and edge orchestration tools like Node-RED.
In an IoT context, this path becomes especially dangerous. A compromised Node.js library in a gateway application could silently exfiltrate sensor data, alter command-and-control logic, or open reverse shells into OT networks. Source validation here comes from cross-referencing Socket.dev’s detailed maintainer reports and technical breakdowns with the Axios GitHub postmortem thread, which consistently match the TTPs documented in Mandiant’s earlier UNC1069 tracking.
The attack surface is not the blockchain; it is the developer toolchain and the people who maintain it.
— DLTA (@DLTA_Sec) April 6, 2026
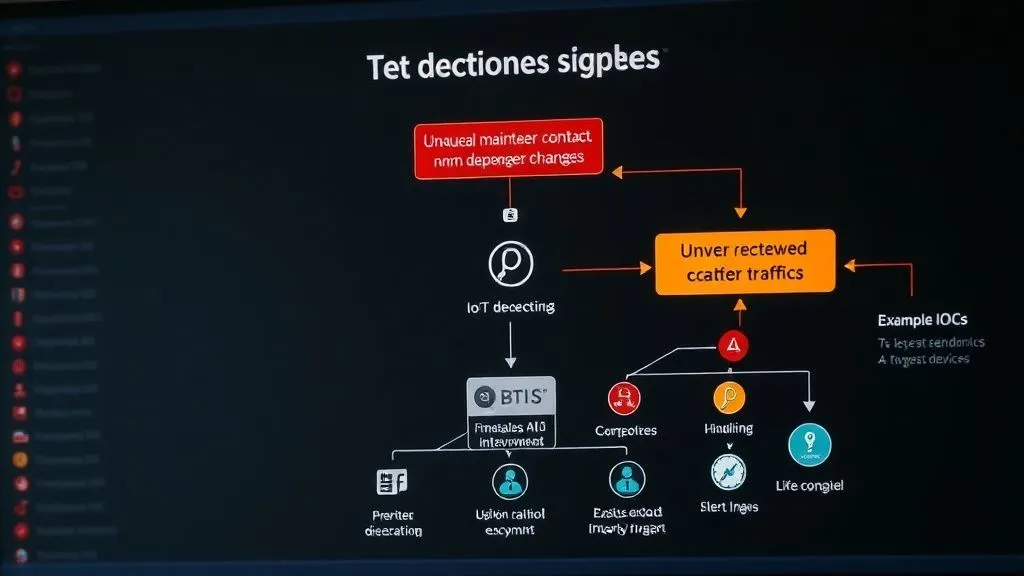
Detection Signals That Matter in Real IoT Environments
Traditional antivirus rarely catches these threats because the initial compromise happens on trusted maintainer systems. Instead, focus on behavioral indicators upstream and downstream.
Watch for maintainers suddenly posting about suspicious outreach or unexplained credential prompts. On the consumption side, scan lockfiles for unexpected version bumps in high-dependency packages like Axios or dotenv. Network-level signals include anomalous outbound connections from IoT gateways-such as repeated calls to unfamiliar domains every 60 seconds, matching the RAT heartbeat observed in the campaign.
Another concrete detail: tools that baseline expected npm publish patterns can flag when a package suddenly includes new postinstall scripts or encrypted payloads. OWASP’s Internet of Things Project further emphasizes monitoring for supply chain anomalies as part of its Top 10 risks, noting that insecure third-party components remain a perennial weak link. Explore the OWASP IoT Project and OWASP Top 10:2025 A03 on Software Supply Chain Failures.
Layered depth here reveals why detection must be continuous: IoT fleets rarely reboot, so a dormant backdoor injected via dependency can persist undetected for months until activated for espionage or disruption.
Practical Controls: A Mapped Framework for IoT Operators
Effective defense requires translating awareness into enforceable steps tailored to resource-constrained IoT teams. The table below maps key controls to their objectives and recommended priority based on blast radius and implementation effort.
| Control | Objective | Implementation Priority |
|---|---|---|
| Generate and validate SBOMs for all software stacks including npm dependencies | Achieve complete visibility into components, versions, and provenance to enable rapid response | High |
| Enforce OIDC-based trusted publishing for npm packages in CI/CD pipelines | Prevent direct maintainer publishes even if credentials are stolen | High |
| Integrate automated dependency scanning (e.g., Socket or OWASP Dependency-Check) in build pipelines | Detect malicious code, license risks, or known vulnerabilities before deployment | High |
| Segment IoT networks from IT/OT with strict firewall rules and zero-trust access | Contain lateral movement if a gateway or edge device is compromised | Medium-High |
| Implement runtime integrity monitoring and firmware signing verification on devices | Ensure only authorized code executes, blocking injected payloads at the device level | High |
These priorities reflect real-world implications: high-priority items address the root cause seen in the Node.js campaign, where a single maintainer breach enabled registry-level distribution. What comes next? Organizations should audit current IoT vendors for SBOM support and mandate it in RFPs, following NIST’s supply chain principles that treat every vendor relationship as a potential breach vector.
A second original insight: while hardware supply chain attacks like BadBox grab headlines, software-layer compromises in languages like Node.js create stealthier persistence because they blend into legitimate update flows. For healthcare IoT or critical infrastructure, this means attackers can achieve espionage-grade access without triggering traditional malware signatures.
Finally, the third synthesis point: with projections exceeding 21 billion connected devices by late 2025, the convergence of state-sponsored maintainer targeting and exploding IoT scale points toward mandatory provenance standards. Expect regulators to extend software bill of materials requirements beyond firmware into runtime dependencies, closing the very gap UNC1069 exploited.
Hypothetical Scenario
Imagine a mid-sized European manufacturer using Node.js-based IoT platforms to monitor assembly-line sensors. One maintainer of a widely used utility package receives a polished LinkedIn outreach from a supposed partner firm. Weeks later, during a seemingly routine video call, the team member runs a “diagnostic” command. Within days, attackers publish a backdoored version that reaches the factory’s edge gateways. Production data begins leaking, and subtle command alterations cause intermittent line stoppages-disrupting output without obvious malware flags. Recovery requires full pipeline rebuilds and credential rotations across hundreds of devices, highlighting how upstream supply chain failures translate directly into operational downtime.
Every IoT operator can act today. Start by inventorying Node.js dependencies in gateways and edge codebases. Rotate tokens, enable OIDC publishing where possible, and embed SBOM generation into release processes. The North Korean campaign is not an isolated event-it is a preview of how determined actors will continue probing the human and technical links that hold IoT together. Prioritizing these controls turns reactive panic into proactive resilience.
North Korean hackers, part of the UNC1069 group, have been targeting high-profile Node.js maintainers using sophisticated social engineering tactics, similar to those used in the Axios supply chain attack.
— Joseph k (@KlinkWow769) April 6, 2026
Disclaimer: This article is for informational purposes only and does not constitute legal, technical, or professional advice. Cybersecurity recommendations should be tailored to specific environments with input from qualified experts. Organizations facing potential incidents should consult official authorities or certified incident response teams.




COMMENTS