**Crypto Security: CanisterWorm's Supply Chain Lessons for Blockchain Defenses** The discovery of CanisterWorm in March 2026 sent rippl...
The discovery of CanisterWorm in March 2026 sent ripples through cybersecurity circles. A financially driven group called TeamPCP unleashed this self-propagating wiper that targets systems based on Iran's timezone or Farsi locale. Yet its real sting for the crypto world lies in the attack methods: poisoned npm packages, cloud misconfigurations, and a command-and-control server hosted on an Internet Computer Protocol (ICP) canister. This incident reveals how everyday tools in Web3 development can become gateways to data destruction. For crypto holders, developers, and exchange operators, it demands a fresh look at threat models where financial gain meets selective destruction.
Threat Model: Hybrid Actors Targeting Crypto's Core Dependencies
TeamPCP operates with clear financial goals since December 2025, harvesting credentials from corporate clouds to enable extortion. Their pivot to a wiper against Iranian systems shows how quickly motives can blend with geopolitical signaling. In crypto security, this hybrid profile fits perfectly. Attackers no longer need nation-state backing to cause irreversible loss. They exploit the same stack crypto teams trust: npm for JavaScript dependencies in dApps, Trivy for vulnerability scanning in pipelines, and cloud platforms hosting 97 percent of their targets on Azure and AWS.
Why does this model hit crypto hard? Private keys and seed phrases often live on developer machines or test environments using these tools. A single breach can expose signing authority for smart contracts or drain liquidity pools. Data from Chainalysis shows over $3.4 billion stolen in crypto hacks during 2025, with centralized services bearing 88 percent of Q1 losses and wallet compromises reaching 158,000 incidents. These numbers, drawn from on-chain tracking and victim reports through early December 2025, remain directly relevant because they highlight the shift toward operational compromises that mirror TeamPCP tactics. The group does not invent new exploits. It automates known ones at scale, turning misconfigured control planes into a worm that spreads silently.
Next step for users: accept that threat actors now treat blockchain infrastructure as both target and weapon. Crypto security must account for actors who destroy data to send messages while quietly siphoning keys elsewhere.
Attack Path: From npm Poison to Blockchain-Backed Wiper
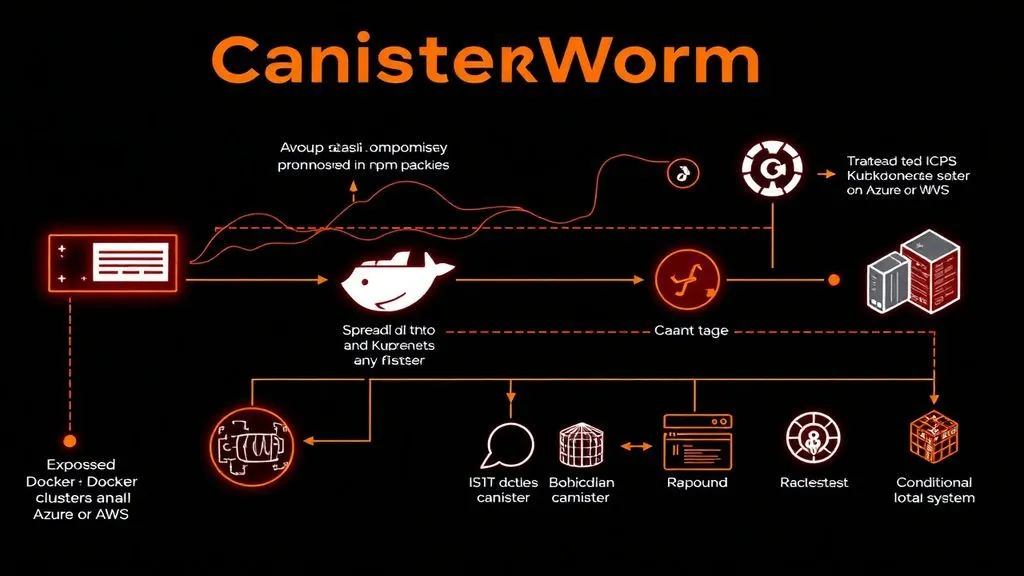
The path begins with supply-chain compromise. TeamPCP injected credential-stealing malware into Trivy and KICS GitHub Actions releases in March 2026. Developers running these scanners in CI/CD pipelines unknowingly pulled tainted packages. Once inside a Node.js environment, the worm establishes background processes disguised as legitimate services. It then scans for exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell flaw to propagate laterally.
Command and control shifts to an ICP canister. This blockchain-based smart contract hosts payloads in a distributed, tamper-resistant way. Operators pay fees in ICP tokens to keep it online, and takedown requires network-wide intervention, not a simple domain seizure. The canister serves the wiper only briefly, sometimes redirecting to a harmless video when inactive. On infected machines matching the Iran criteria, the payload checks for Kubernetes access. If present, it wipes every node in the cluster. Otherwise, it runs the equivalent of rm -rf / --no-preserve-root, erasing local data without recovery options.
This sequence shows deliberate layering. Initial access via dev tools leads to cloud footholds, then blockchain C2 evades traditional blocks. For crypto projects relying on similar pipelines, one poisoned dependency can cascade into full protocol compromise. Independent validation across Aikido's teardown, Wiz reports on the KICS incident, and KrebsOnSecurity coverage confirms the mechanics without contradiction.
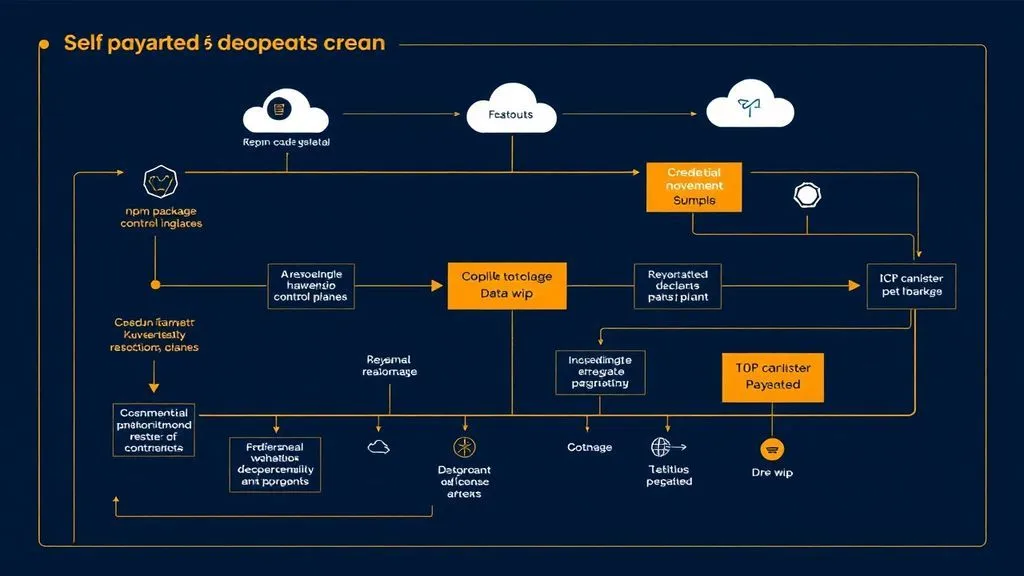
In a hypothetical scenario, a mid-sized DeFi team updates Trivy during a routine audit of their liquidity pool contracts. The package pulls a hidden shell that exfiltrates GitHub tokens. Within hours the worm reaches their staging Kubernetes cluster. When the wiper activates on a developer's machine with a test wallet, seed phrases vanish before offline backups complete. Recovery requires rebuilding the entire environment from scratch while attackers monitor for real-key exposure.
Detection Signals: Beyond Signature-Based Alerts
Traditional antivirus misses CanisterWorm because it avoids disk writes where possible and uses fileless execution in memory. Watch for these concrete signals instead. Unusual GitHub Action commits or tag poisoning on popular repos signal early supply-chain tampering. Spikes in outbound traffic to unknown ICP canister addresses, especially during build processes, indicate C2 communication. Processes masquerading as system services but scanning memory for tokens like GitHub PATs or AWS keys deserve immediate scrutiny.
Locale-based triggers add another layer. Logs showing sudden rm or wipe commands tied to timezone checks point to conditional payloads. Cloud platforms should flag anomalous kubectl usage or Redis credential dumps. Cross-reference with Flare's profiling of TeamPCP shows these patterns repeat across Azure-heavy environments. Crypto teams gain an edge by routing all CI/CD traffic through monitored proxies that log blockchain interactions separately from normal API calls.
What follows detection? Isolate the affected pipeline immediately, revoke tokens, and audit every downstream package. Ignoring these signals lets the worm turn a single dev workstation into a launchpad for broader ecosystem damage.
Controls: Prioritized Mapping for Crypto Environments
Effective defense requires mapping controls to the exact risks exposed here. The table below translates the attack path into actionable layers, with priority based on implementation effort versus impact in crypto pipelines.
| Control | Objective | Implementation Priority |
|---|---|---|
| Enforce npm audit, lockfiles, and SBOM generation in every CI/CD run | Block poisoned dependencies before they reach production builds | High |
| Harden cloud control planes: disable public Docker APIs, use private Kubernetes endpoints, and enable Redis authentication with network ACLs | Prevent initial worm entry and lateral movement across exposed services | High |
| Monitor and block anomalous ICP canister traffic at network level; treat blockchain C2 as high-risk | Detect and disrupt resilient command-and-control hosted on decentralized protocols | Medium |
| Require air-gapped hardware wallets for all production keys and maintain encrypted, multi-region offline backups | Protect seed phrases and signing material from local wiper destruction | Critical |
| Implement memory scanning and process anomaly detection in developer endpoints using tools like TruffleHog for credential validation | Identify fileless credential harvesting before exfiltration | Medium |
Each control builds resilience. SBOM generation, for instance, creates a verifiable bill of materials that flags changes in Trivy-like tools instantly. Air-gapped wallets ensure even total machine compromise leaves funds untouched. Prioritize high-impact items first because crypto's always-on nature leaves no room for delayed patching. Test these in staging, then roll out with minimal disruption to trading or protocol uptime.
Future Trends and User-Centric Takeaways
CanisterWorm marks a shift. Crime groups now repurpose blockchain resilience for evasion, just as North Korean actors embedded IT staff in exchanges to steal $2.02 billion in 2025 alone. Original insight one: this democratizes nation-state tactics, meaning crypto security teams must scan all on-chain traffic for malware indicators rather than assuming decentralization equals safety. Insight two: tools built for crypto defense, such as vulnerability scanners, have become prime supply-chain targets, creating ironic blind spots that require independent verification layers. Insight three: conditional wipers prove attackers can regionalize risk; global users in any jurisdiction should treat data loss as a baseline outcome and design recovery around geographic diversity.
CanisterWorm targeting systems with Iran's timezone or Farsi as default language is the part of the TeamPCP story that should make every IR team reconsider their assumptions about actor motivation. ... Update the box.
— 4A 45 56 49 4C (@4A4556494C) April 3, 2026
Practical next steps cut across roles. Individual holders should verify every wallet interaction offline and store seeds on paper or metal in multiple secure locations. Development teams must sign all releases and run dependency checks before merge. Exchanges and custodians need to segment CI/CD from production signing environments. These steps move beyond awareness into hardened posture.
TeamPCP's brief campaign, validated through Aikido's real-time analysis, KrebsOnSecurity reporting, and Chainalysis on-chain data, proves one point clearly. Crypto security succeeds when controls address the full path from dependency to destruction. Ignore the signals, and the next worm may not wait for a geopolitical trigger.
Disclaimer: This article discusses sensitive cybersecurity topics for educational purposes only. It does not constitute legal, financial, or professional advice. Consult qualified experts for your specific situation. Always verify sources and implement controls responsibly.




COMMENTS